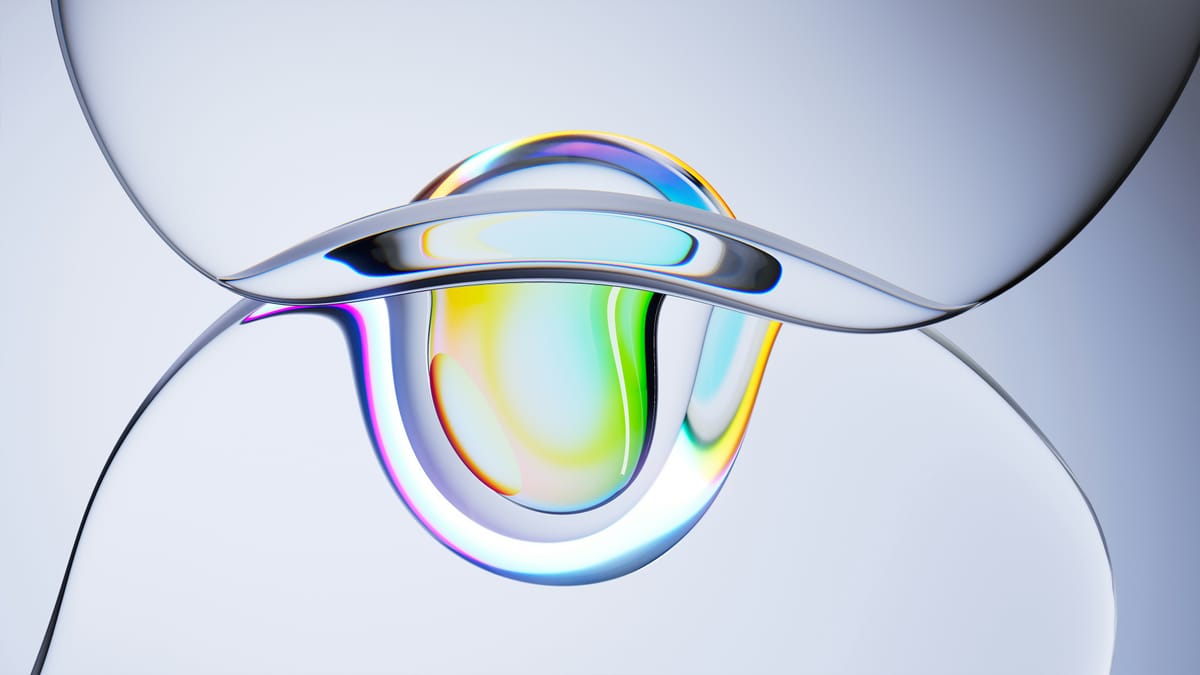
Deep Dive: Humans to Test Underwater Habitat in 2025

British startup Deep is pioneering underwater living with its Sentinel project, a modular habitat slated for completion in 2027. Utilizing advanced 3D printing and welding, Sentinel will enable scientists to live and work at depths up to 200 meters for extended periods. A smaller, transportable habitat called Vanguard, launching in 2025, will serve as a testbed. Vanguard can house three divers for up to a week, demonstrating the potential to dramatically increase the efficiency of ocean research and enhance our understanding of marine ecosystems in the face of climate change.
Read more