The Hunt for the Legendary Hacktoberfest Tees

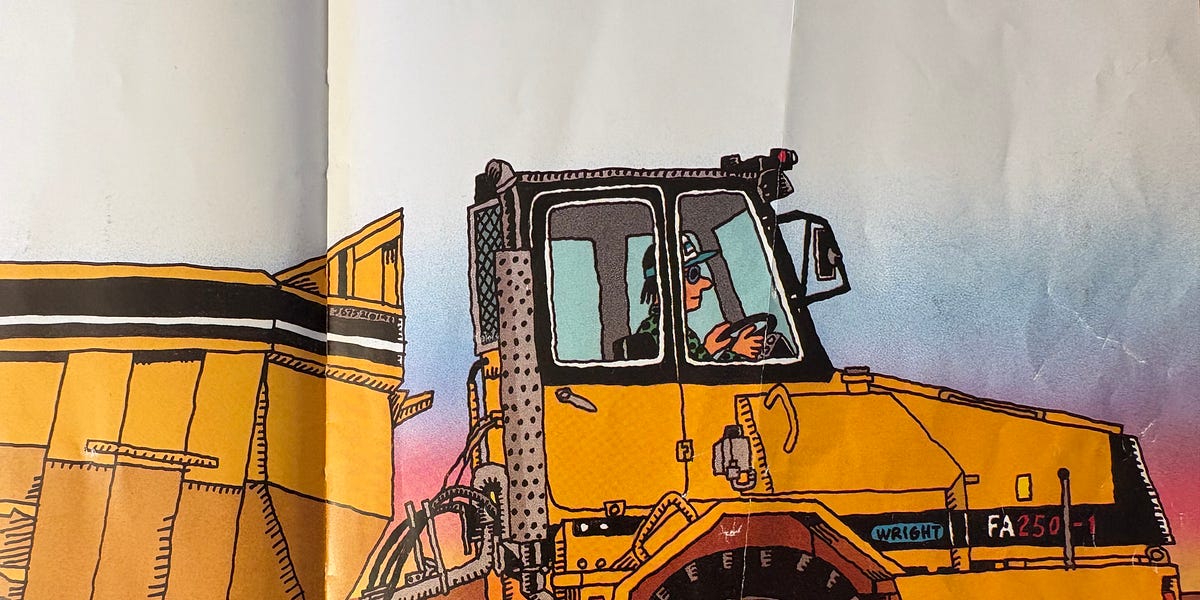
A developer's quest to recreate their beloved, worn-out Hacktoberfest t-shirts leads them on a frustrating search for high-resolution design assets. After years of wearing the free shirts given for participation, they're now trying to reproduce them but struggle to find suitable images online. Low-resolution images, AI upscaling failures, and missing years of designs are all part of the journey. The author pleads for help from the community to locate the missing high-resolution logos.
Read more