IndiGo's Near-Monopoly in India's Domestic Aviation Market
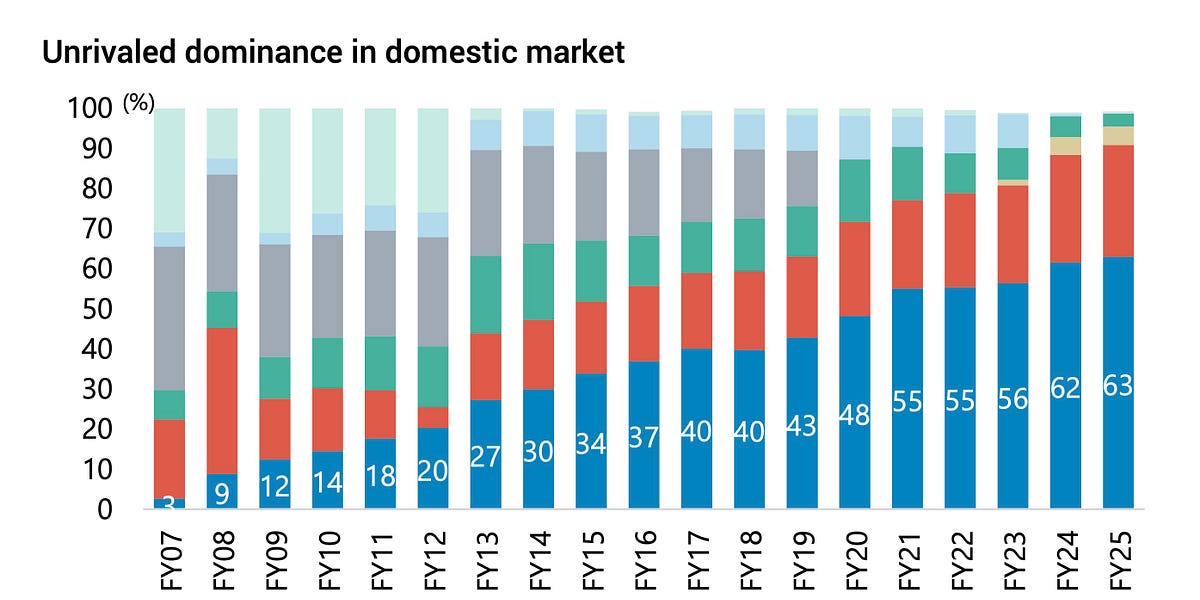
India's domestic aviation market is dominated by IndiGo, holding a staggering 64.4% market share. This dominance, achieved through a decade of expansion and the struggles of competitors like SpiceJet and Air India, sees IndiGo holding a near-monopoly on 66% of its routes. Despite slowing demand and price pressures, IndiGo's low-cost model and international expansion strategy are strengthening its position. However, navigating reduced demand and pricing power from a near-monopolistic position presents significant challenges.
Read more