AI-Powered Quant Trading Lab: Bridging Theory and Practice

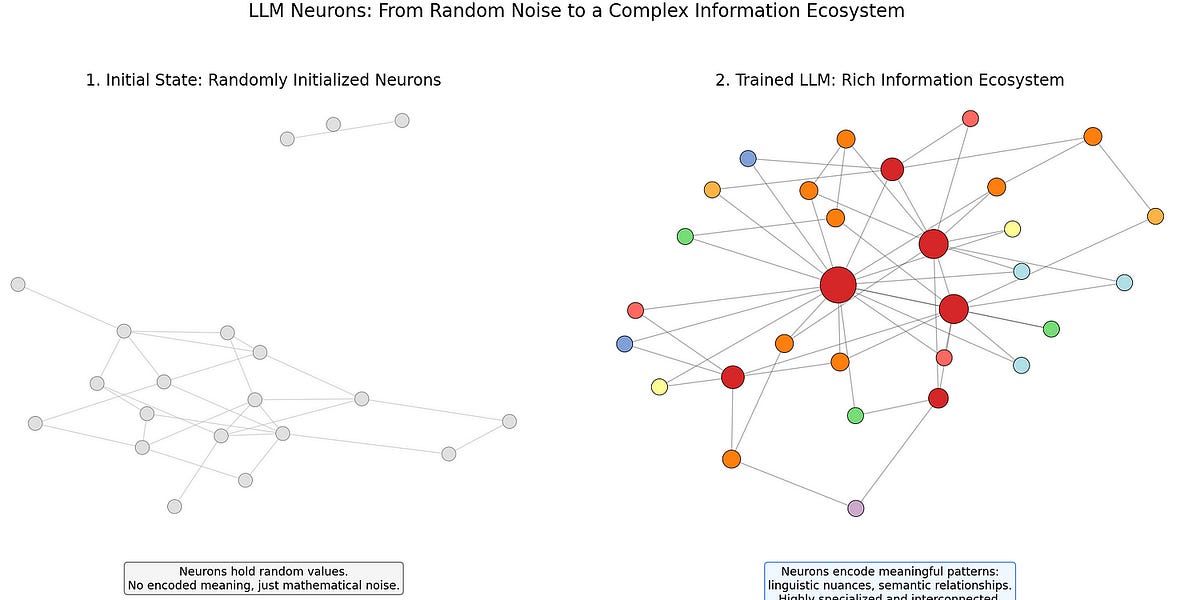
A research lab is building an AI-driven quantitative trading system leveraging the complex, data-rich environment of financial markets. Using first principles, they design systems that learn, adapt, and improve through data, with infrastructure built for rapid iteration, real-time feedback, and a direct link between theory and execution. Initially focusing on liquid markets like equities and options, their aim transcends better modeling; they seek a platform for experimentation where every result refines the theory-practice loop.
Read more