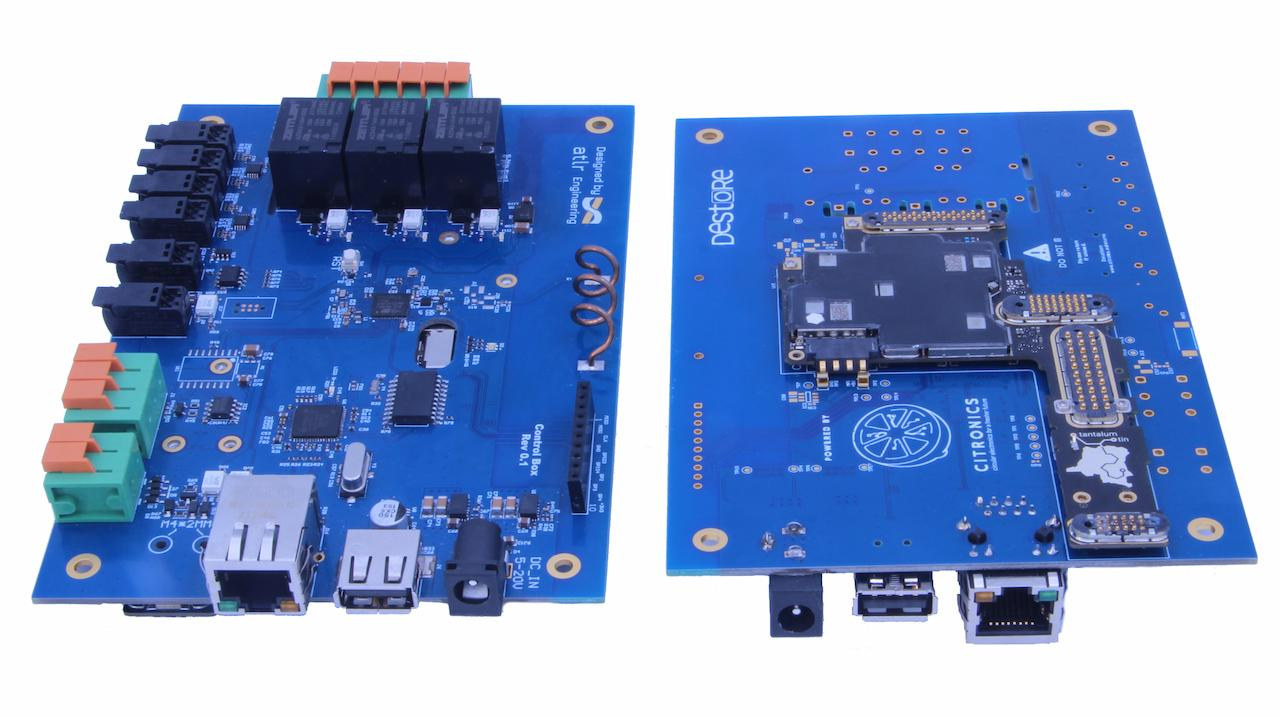
PostgreSQL 18 Beta: UUIDv7 Makes Database Primary Keys Better

PostgreSQL 18 Beta is out, and its most anticipated feature is native support for UUIDv7. UUIDv7, a timestamp-based UUID variant, solves the sorting and index locality issues inherent in traditional UUIDs used as database primary keys. It offers a compelling combination of globally unique identifiers and temporal ordering, making it ideal for distributed databases needing high performance and scalability. Other performance improvements in PostgreSQL 18 include async I/O and index optimizations.
Read more