Building a WebAssembly VM in C: A Six-Month Side Project Retrospective
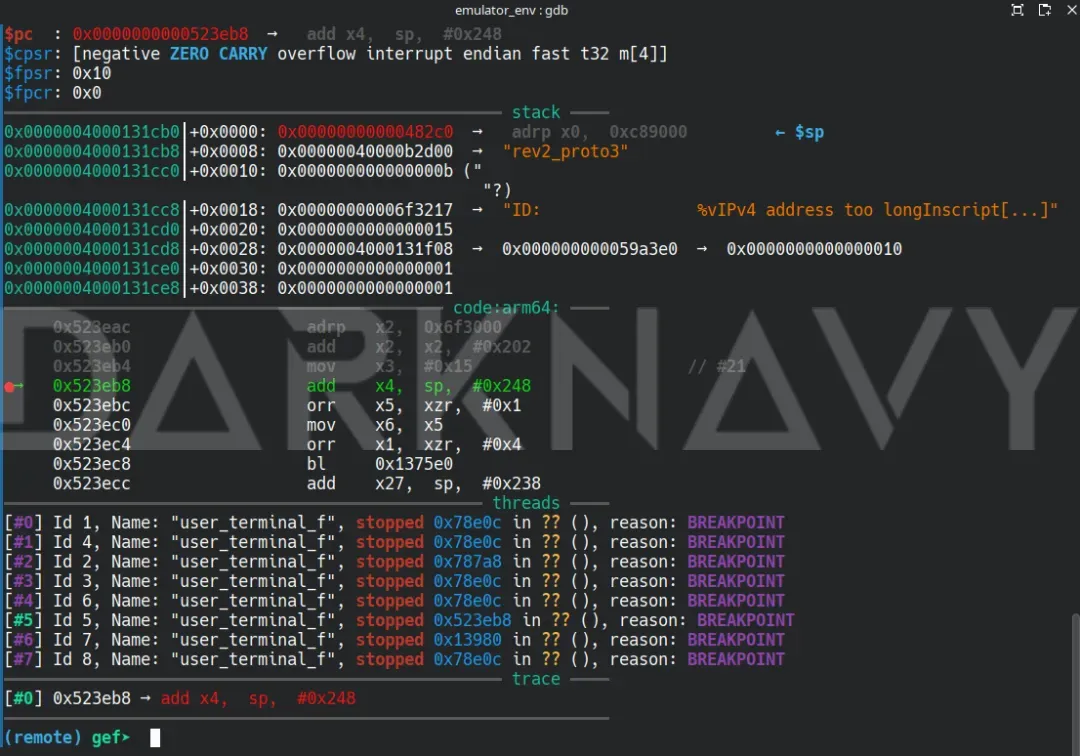
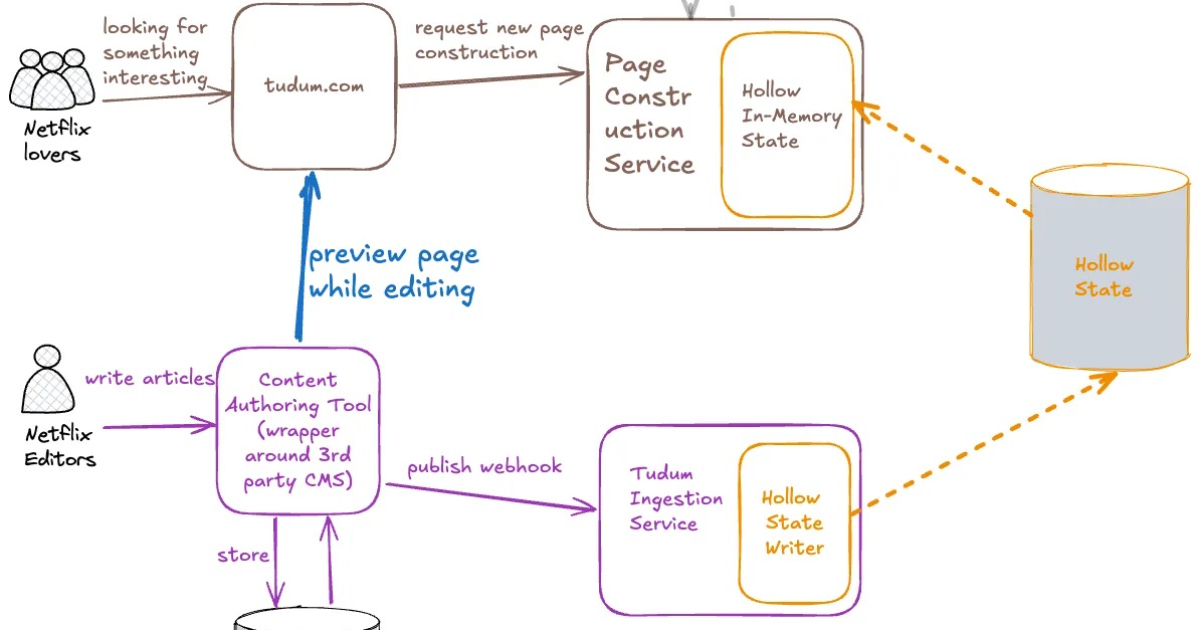
Over six months, the author dedicated their spare time to building a WebAssembly virtual machine in C, called Semblance. This project provided a much-needed break from the cycle of short-lived side projects and allowed for a deep dive into the WebAssembly core specification. The article details the architecture, covering module decoding, import resolution, module instantiation, and instruction execution. The author shares challenges and learnings, culminating in a successful "Hello, World!" execution. This project not only boosted the author's skills but also provided a strong foundation for future contributions to industrial-grade runtimes.
Read more