The Nucleus: A Metabolic Compartment Rewriting Cell Fate
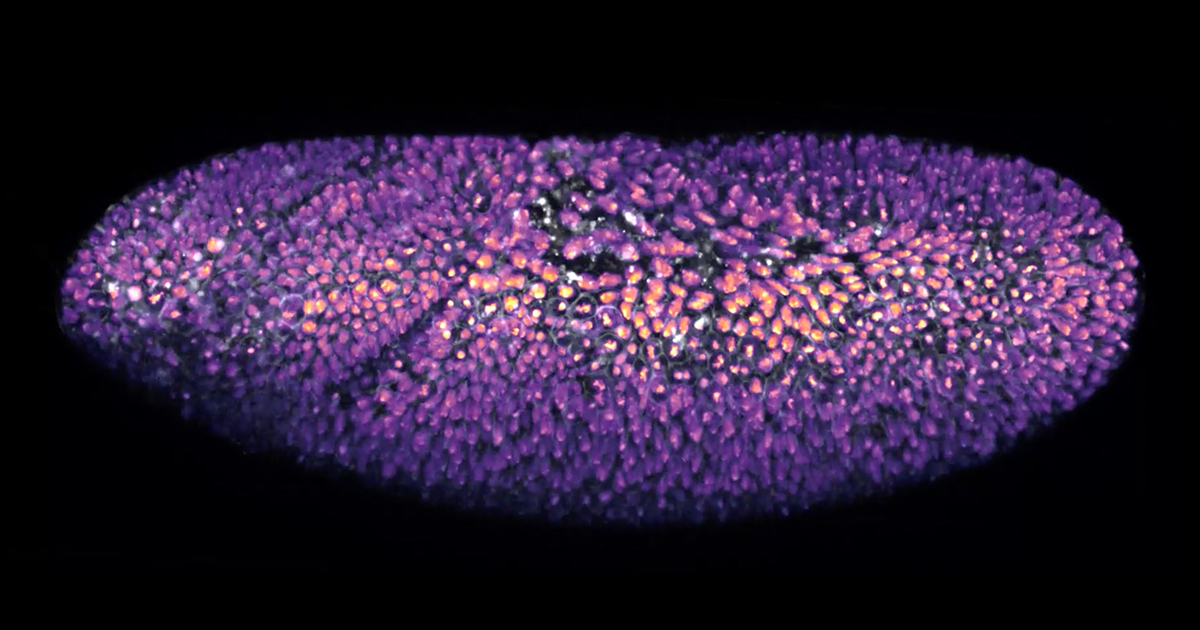
A groundbreaking study reveals the cell nucleus as a unique metabolic compartment, distinct from other cellular regions, playing a pivotal role in gene expression and cell fate. Researchers discovered that metabolic enzymes within the nucleus dynamically regulate epigenetic marks, such as histone acetylation, which change based on nutrient availability. In early embryonic development, nuclear metabolic activity is crucial for cell differentiation, while metabolites like alpha-ketoglutarate are key players in both stem cell differentiation and cancer suppression. This discovery opens exciting avenues for cancer therapy, suggesting the possibility of manipulating cellular metabolism to alter cell fate and treat diseases stemming from abnormal cell differentiation.