Baldur's Gate 3 Native Steam Deck Build: Save & Mod Migration Guide
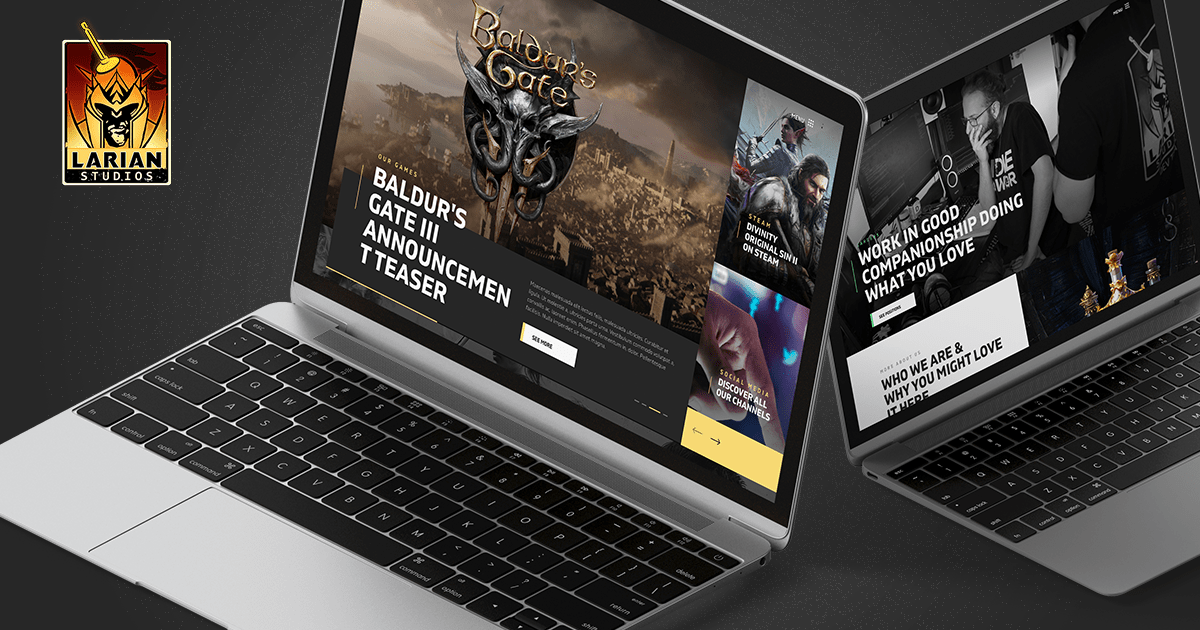
The Baldur's Gate 3 update on Steam Deck brings a native version, improving performance. However, save game and mod locations change. Steam Cloud saves will automatically migrate; otherwise, manually copy saves to `/home/deck/.local/share/Larian Studios/Baldur's Gate 3/PlayerProfiles/Public`. Mod migration depends on your Larian account and mod.io connection; manually copy mods if not connected.
Read more