A Journey to Optimize Cloudflare D1 Database Queries

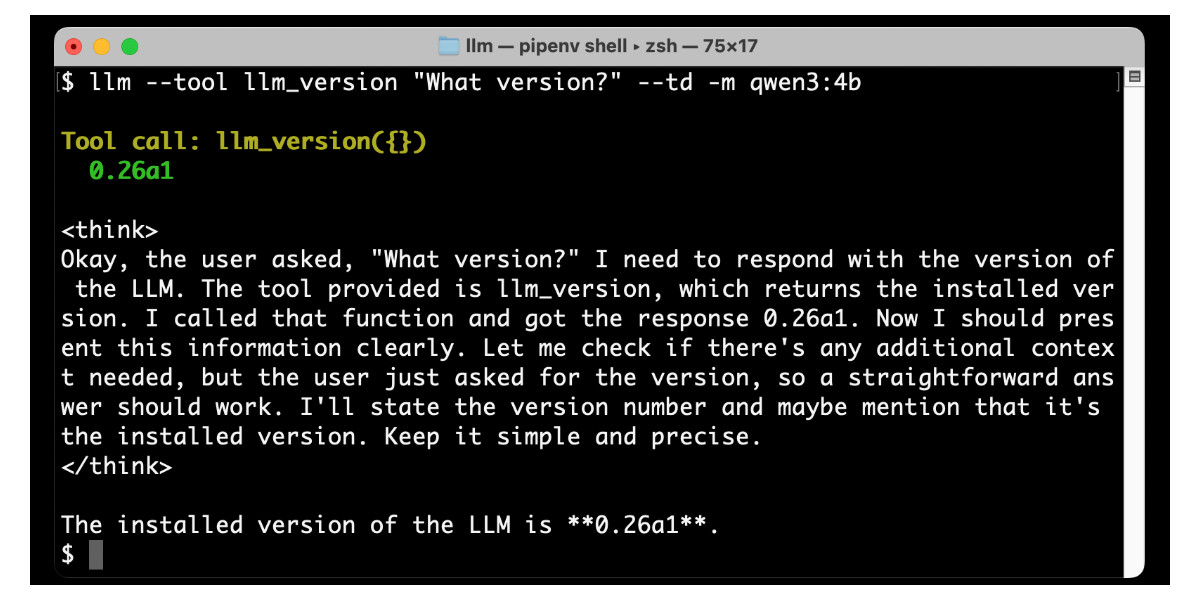
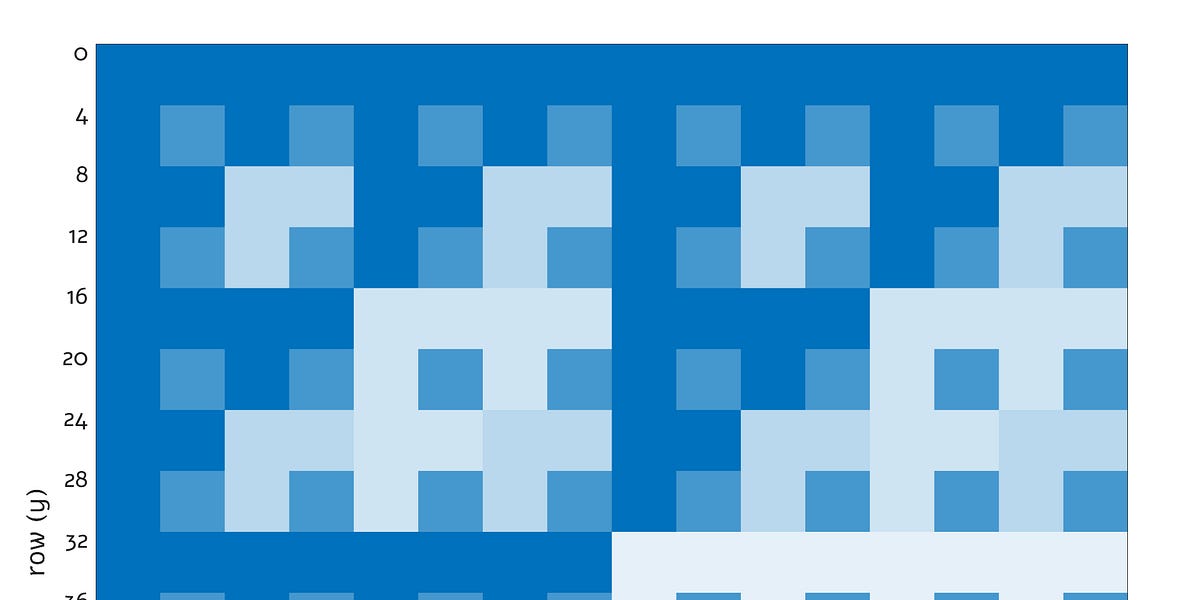
A frontend developer encountered performance bottlenecks while using Cloudflare Workers and the D1 database. By monitoring the D1 dashboard, examining query statements, and analyzing row read/write counts, they identified several key issues: slow single queries, inefficient batch writes, unnecessary row reads due to including IDs in update operations, full table scans from count queries, Cartesian product explosions from multi-table joins, and suboptimal bulk inserts. Solutions involved leveraging D1 batch operations, excluding IDs from updates, implementing cursor-based pagination, splitting multi-table join queries, and optimizing bulk insert statements. These optimizations drastically improved query performance, reducing execution time from 78ms to 14ms in some cases. The experience highlights the importance of continuous monitoring, iterative optimization, and the crucial differences between server-side and client-side performance issues.
Read more