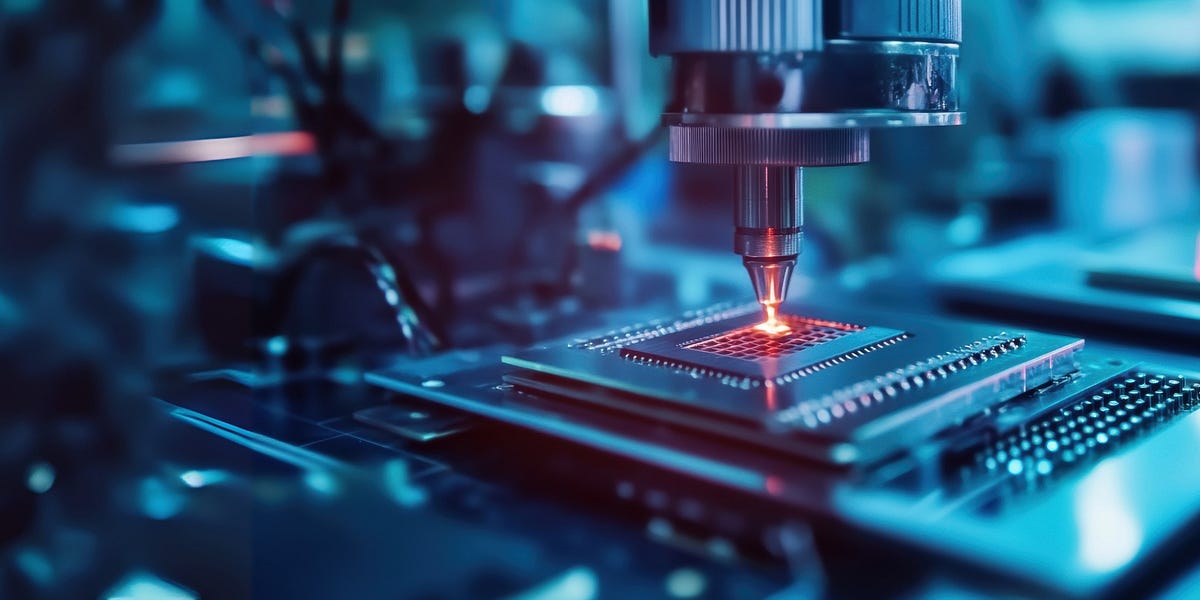
Progressive JSON: Streaming Data Like a Progressive JPEG
This article explores progressive JSON, a method to improve JSON data transfer efficiency. Traditional JSON requires waiting for the entire data load before parsing, unlike progressive JSON, which resembles progressive JPEGs by first transmitting the data framework and then progressively filling in details. The article compares depth-first and breadth-first data streaming, noting that React Server Components (RSC) utilize a breadth-first approach combined with Suspense components to achieve progressive UI loading, enhancing user experience.
Read more