Apple's Closed Ecosystem Holds Back AI-Powered iOS Development
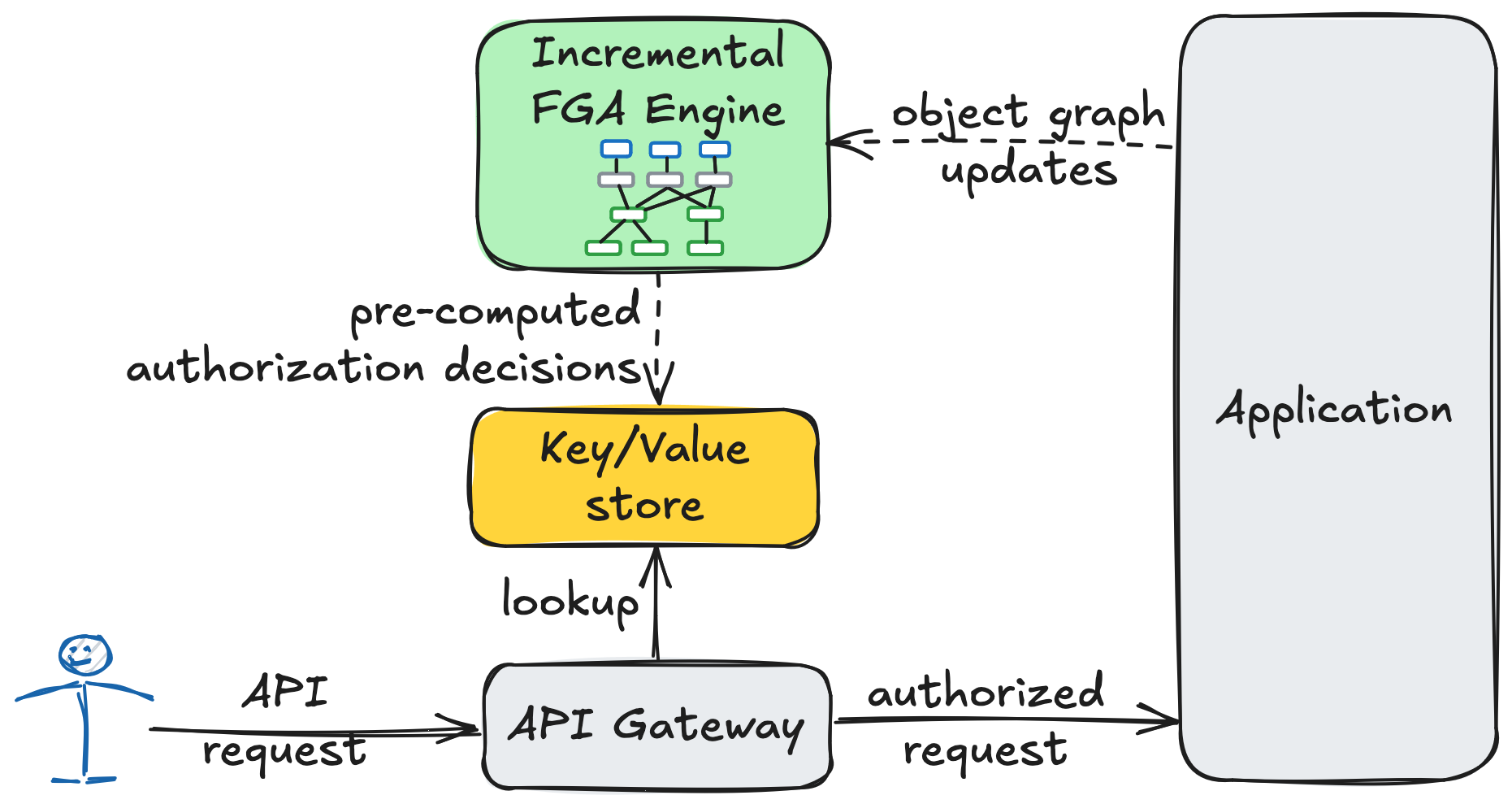
A veteran iOS developer laments Apple's closed-source ecosystem, hindering its ability to compete with AI-powered app building platforms like lovable.dev and a0.dev. The article highlights the complexities of iOS compilation, proprietary Xcode project formats, the closed-source nature of SwiftUI, and the challenges of deploying macOS servers at scale as significant roadblocks to developing robust AI-assisted iOS development tools. In contrast, Android's open-source nature provides a significant advantage in AI app development. The author argues that Apple's long-standing neglect of developer experience has ultimately left them behind in the AI race.
Read more