InspectMind AI: Hiring AI Engineers for 100x Productivity Boost in Construction

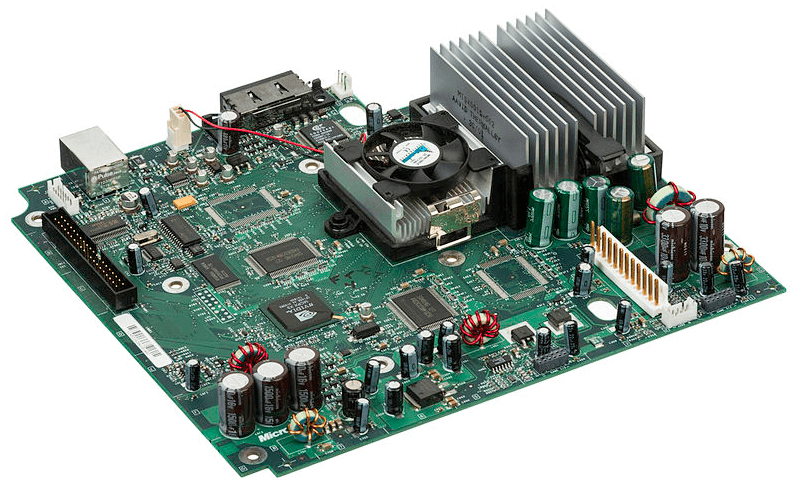
InspectMind AI is building AI applications to revolutionize inspections in construction, real estate, and infrastructure. They're looking for experienced full-stack engineers to join a team of experts from Google, Airbnb, and top universities. The role involves designing and building end-to-end AI solutions, integrating with hardware like smart glasses, and leveraging cutting-edge LLM technology. This is a fast-paced environment with a focus on rapid iteration and direct customer interaction.
Read more