:quality(75)/https%3A%2F%2Fassets.lareviewofbooks.org%2Fuploads%2FSuperbloom-1.jpg)
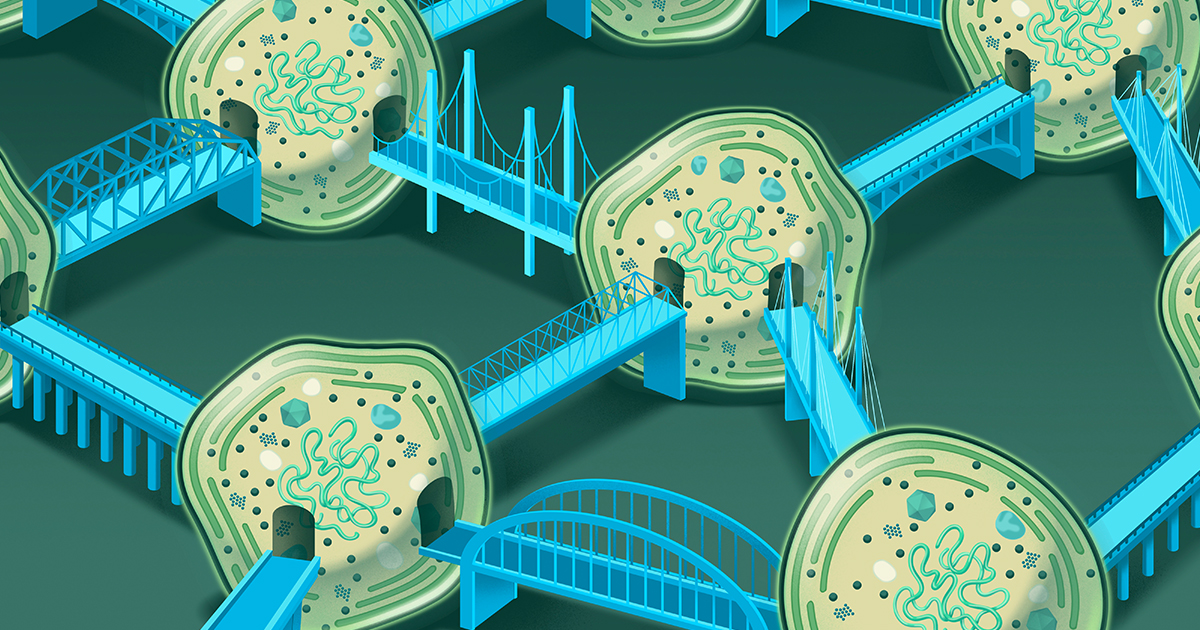
Nicholas Carr's new book, *Superbloom*, examines how modern connection technologies—cell phones, the internet, social media, etc.—impact individuals and society. Carr argues these technologies aren't inherently evil but cause negative consequences due to our misconceptions about communication and ourselves. He uses the 2019 Los Angeles poppy bloom event to illustrate how information overload and social media's amplification effect lead to chaos and negativity. The book traces the history of communication technologies, highlighting how they've always been accompanied by supernatural imaginings, and raises concerns about anonymity, power, and information veracity. Carr critiques technological optimism, arguing that information overload hasn't led to a more democratic or rational society but has instead exacerbated social divisions. He contends that social media's design leverages cognitive biases, exacerbating information fragmentation and fast-paced thinking, ultimately resulting in a 'hyperreality' where truth is indistinguishable from falsehood. Carr calls for a return to reality, resisting information overload, and proposes potential solutions, such as increasing the friction cost of information dissemination.
Read more


:quality(75)/https%3A%2F%2Fassets.lareviewofbooks.org%2Fuploads%2FSuperbloom-1.jpg)