Saying Goodbye to try_files: Optimizing Nginx Performance

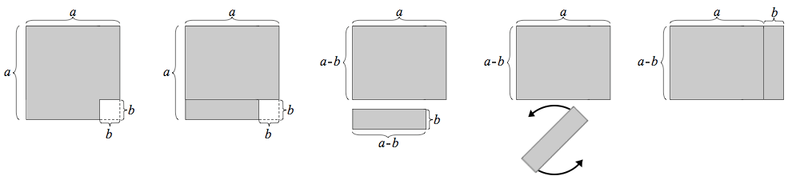
This article delves into the performance implications of the try_files directive in Nginx. While try_files handles SEO-friendly URLs, it incurs unnecessary disk I/O for file existence checks, impacting performance. The article advocates for a framework-specific approach (e.g., leveraging WordPress's /wp-content/ directory) to configure Nginx directly, allowing Nginx to serve static files without try_files. A Python script is also provided to automate the generation of Nginx location blocks for various static file types, further enhancing efficiency and security.
Read more