Anscombe's Quartet: Why Data Visualization Matters

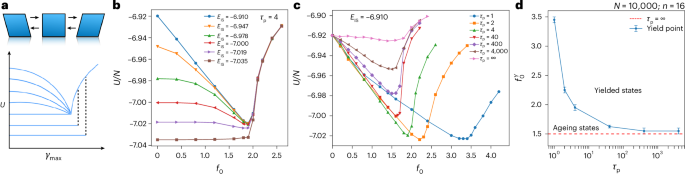
Anscombe's quartet is a classic statistical example illustrating the importance of data visualization. Four datasets with nearly identical descriptive statistics reveal drastically different distributions and visual appearances. This highlights the inadequacy of relying solely on summary statistics and emphasizes the need to graph data before drawing conclusions. The quartet demonstrates how outliers and influential observations can significantly skew statistical properties, underscoring the crucial role of visual analysis in understanding data.
Read more