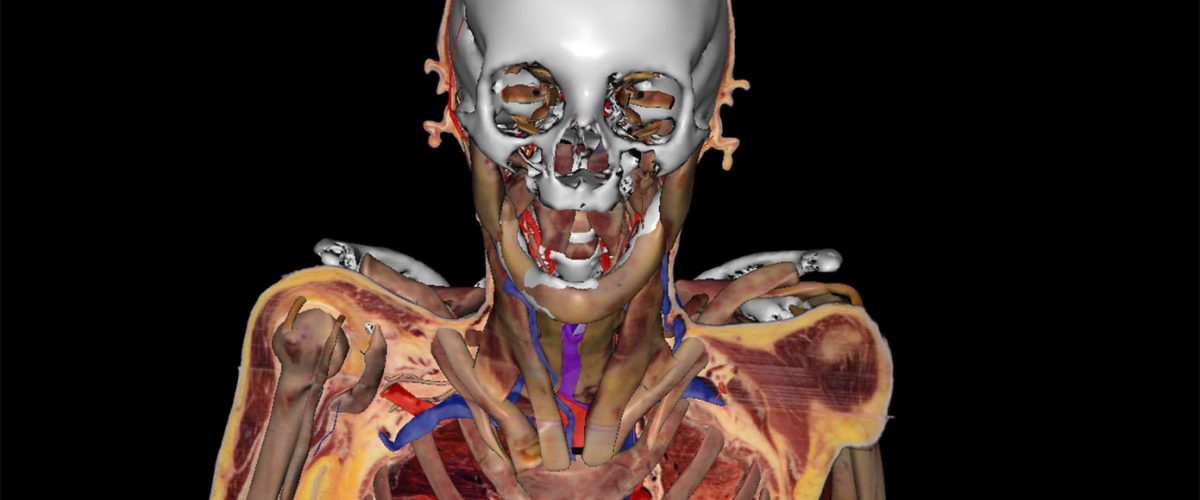
The slowdown of Moore's Law has led to increasing power density in chips, making heat dissipation a critical bottleneck affecting performance and lifespan. Traditional cooling methods are insufficient for future high-performance chips, such as the upcoming CFET transistors. Researchers have developed a new simulation framework to predict how new semiconductor technologies affect heat dissipation and explored advanced cooling techniques, including microfluidic cooling, jet impingement cooling, and immersion cooling. System-level solutions, such as dynamically adjusting voltage and frequency, and thermal sprinting, also aim to balance performance and heat. Future backside functionalization technologies (CMOS 2.0) like backside power delivery networks, backside capacitors, and backside integrated voltage regulators, promise to reduce heat by lowering voltage but may introduce new thermal challenges. Ultimately, solving the chip heat problem requires a multidisciplinary effort, with system technology co-optimization (STCO) aiming to integrate systems, physical design, and process technology for optimal performance and cooling.
Read more