800,000 Roman Nails: A Buried Secret of the Empire

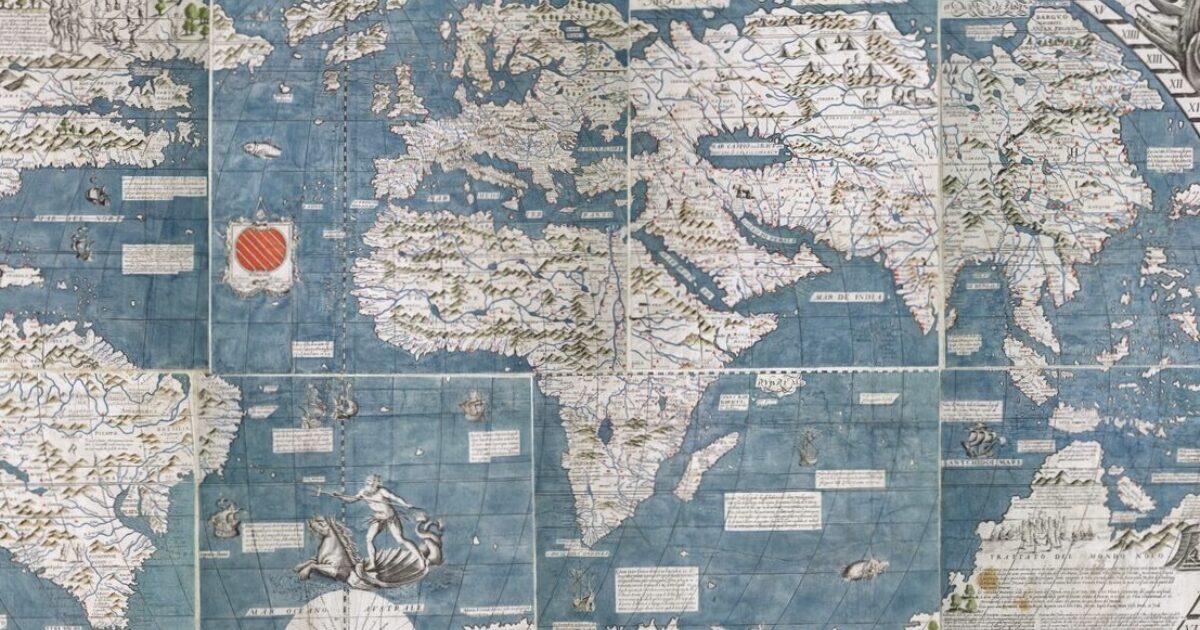
In 1959, the excavation of the Roman fort at Inchtuthil, Scotland unearthed an astonishing hoard: over 800,000 Roman nails! Ranging in size from small carpentry nails to massive spikes, the remarkably preserved nails were buried in a deep pit. This wasn't a result of meticulous Roman fort dismantling, but a hasty burial during a rapid retreat, designed to prevent the valuable iron from falling into the hands of local tribes. The discovery reveals not only the scale of Roman legionary construction but also the urgency and strategic shifts of the empire's withdrawal, offering a glimpse into a little-known historical episode.