The Return of Network Effects in the Age of GPT Wrappers
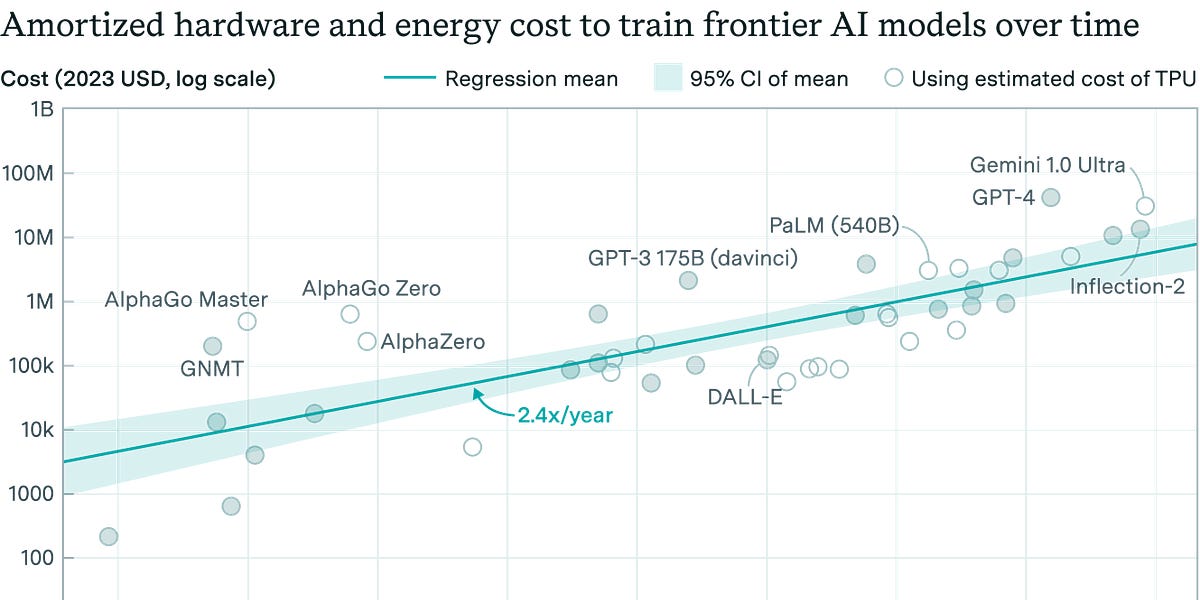
This article challenges the prevailing theory of AI defensibility, which posited that the high cost of training large language models would create a significant barrier to entry. The author argues that as AI becomes ubiquitous, network effects will become paramount. Drawing parallels to the Web 2.0 era, simple 'GPT wrapper' applications can achieve sustainable competitive advantage by building user networks, enhancing engagement, and optimizing monetization strategies. This will drive a fusion of network effects and AI capabilities, reshaping the competitive landscape.
Read more



/cdn.vox-cdn.com/uploads/chorus_asset/file/25831342/c0d500b2_f7b9_41f7_9d77_9b1fa783a533_1.eed9aefe2ef3349c8007b16fbf1d50a1.jpeg)