Wind-Powered Knitting: A Mobile Factory Harnessing Urban Winds
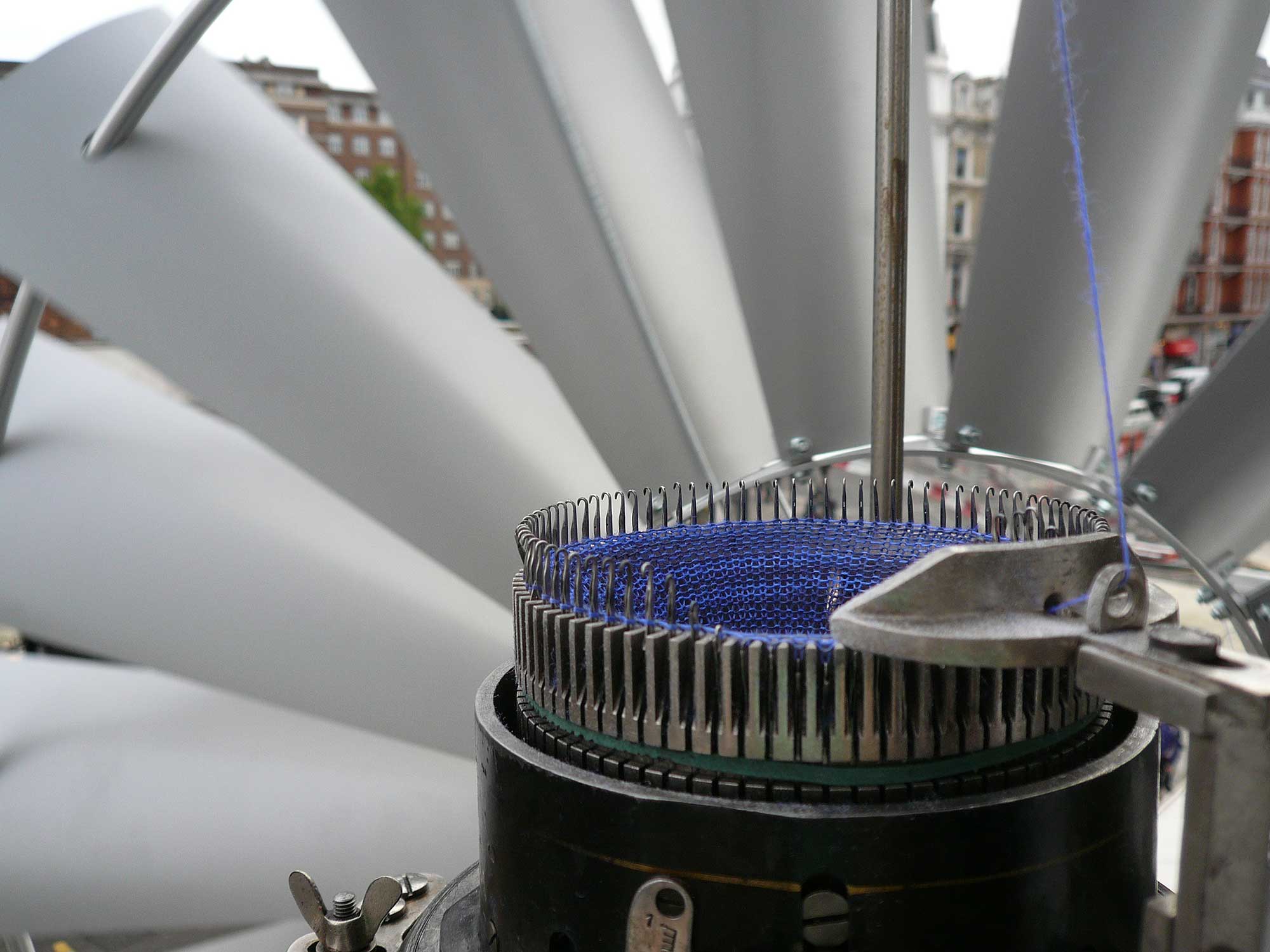
Imagine a building facade with a constantly growing knitted fabric, a 'mobile factory' powered by wind. Wind propels the knitwear down from the building's top, through a window into the interior, where it's eventually 'harvested' into scarves labeled with their creation time. This art installation cleverly connects public and private space, showcasing the potential of harnessing urban wind energy and uniquely visualizing the production process.
Read more