Rediscover the Joy: Building Personal Websites in the Age of AI
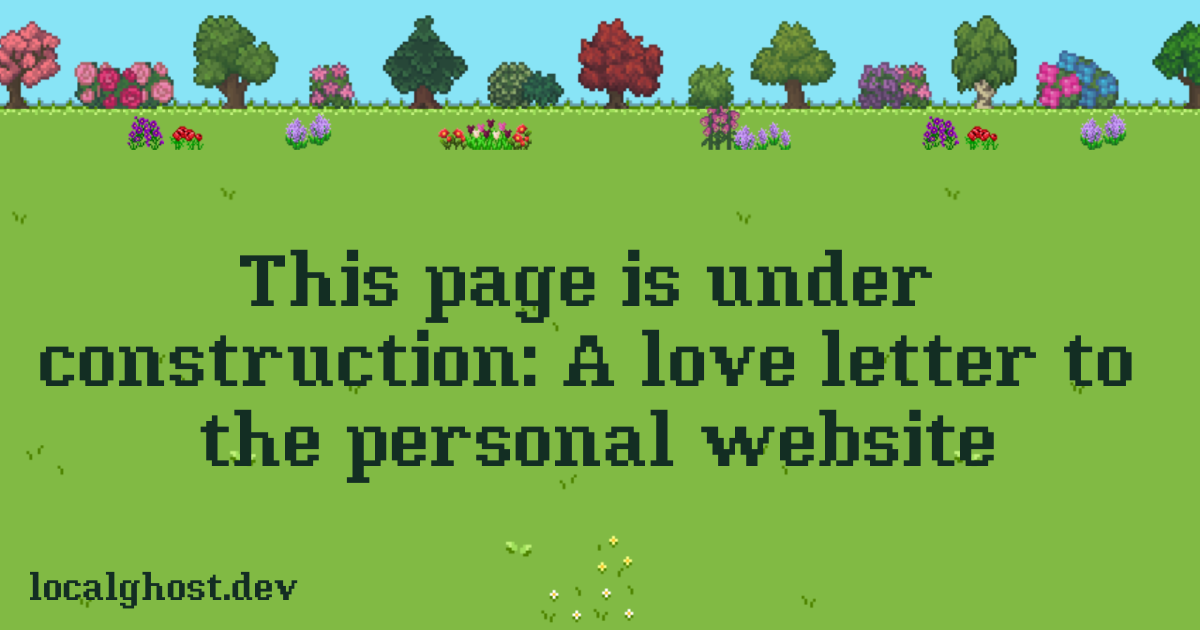
The author calls for a return to building personal websites as a counterpoint to today's commercialized and centralized web. The article contrasts the individuality of early websites with the homogeneity of modern corporate sites and the data privacy concerns of relying on large platforms. Readers are encouraged to create unique online spaces driven by personal interests, reclaiming control over their content. Convenient website-building tools and platforms like Neocities are recommended. The piece reflects a longing for a more decentralized web and a celebration of independent creation.
Read more