Fighting Back Against Windows 11's Built-in Malware: An Open Source Counter-Offensive
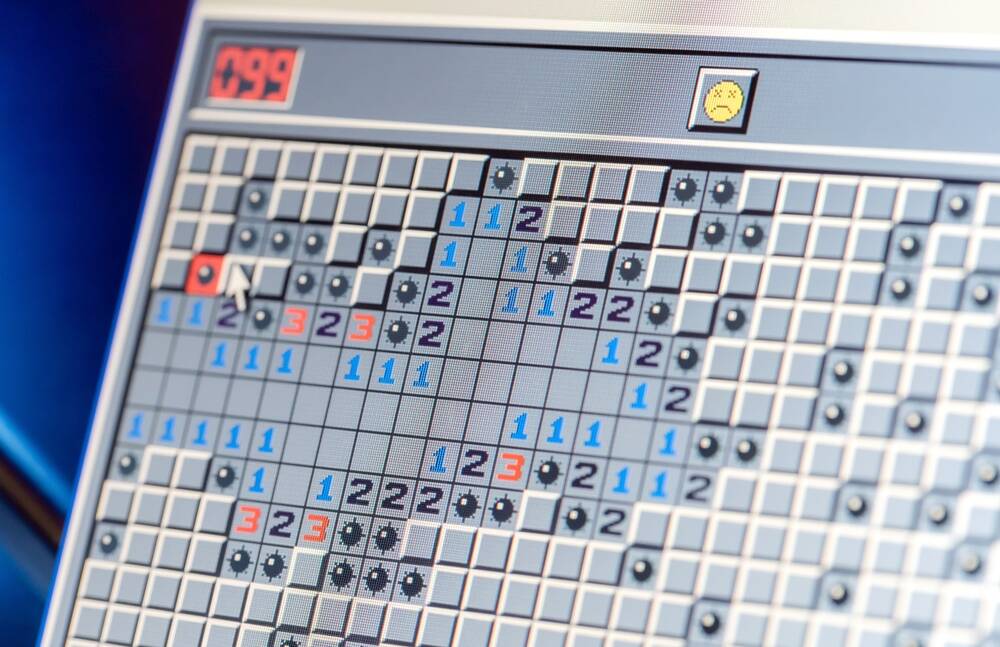
Windows 11 is riddled with distracting ads and tracking features, akin to built-in malware. This article calls for the development of an automated Windows cleanup tool to counter Microsoft's tactics. The tool should be open-source, user-friendly, configurable, and integrate existing excellent tools. The ultimate goal is to force Microsoft to change course and improve user experience through community pressure; a prime example of FOSS fighting back against Microsoft's dominance.
Read more