Preservation Project Completes: All 54 iPod Clickwheel Games Saved
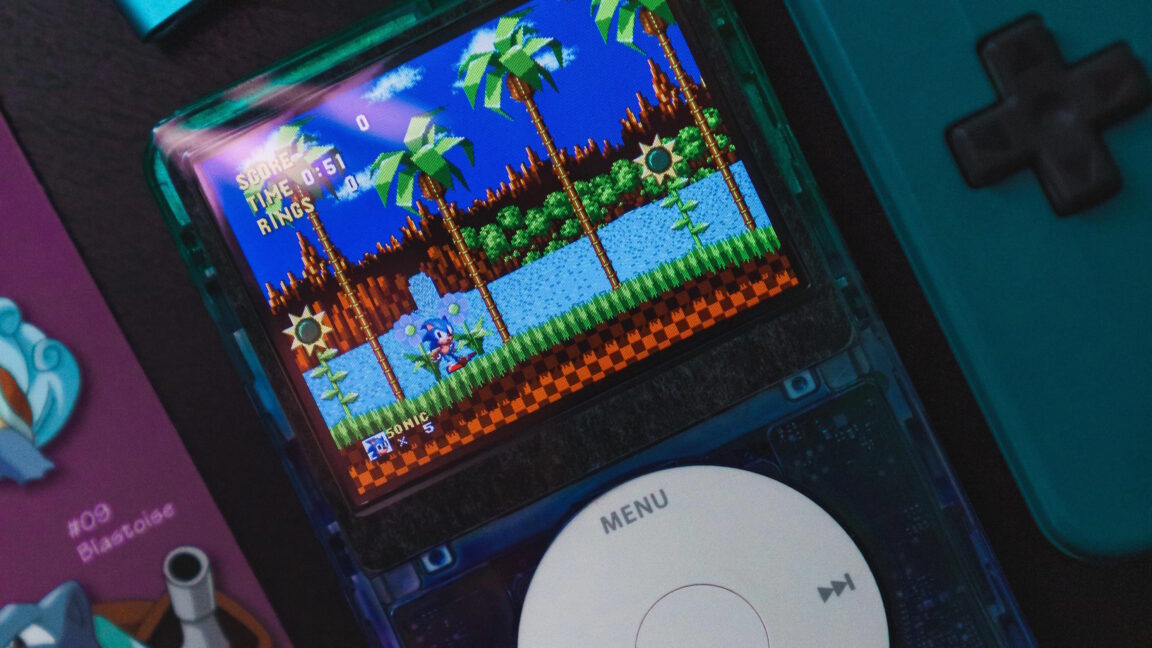
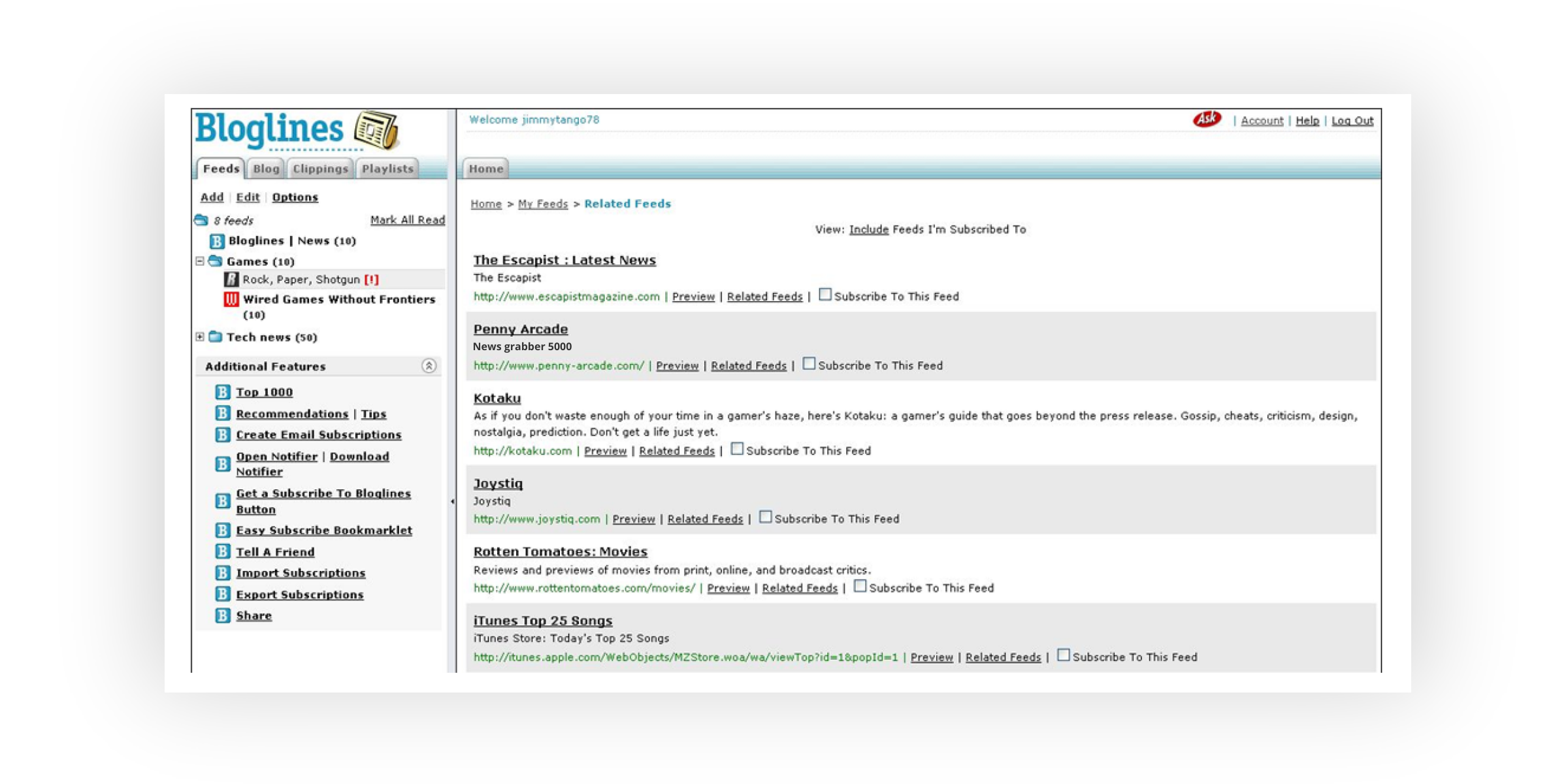
A community project dedicated to preserving classic iPod clickwheel games has finally reached its goal after over a year of effort. By coordinating multiple iPod users' iTunes accounts, the project overcame Apple's FairPlay DRM and successfully collected and preserved all 54 official games. The project faced numerous technical challenges and setbacks, but the final piece, Real Soccer 2009, was eventually provided by a user, completing the archive.
Read more


.png)