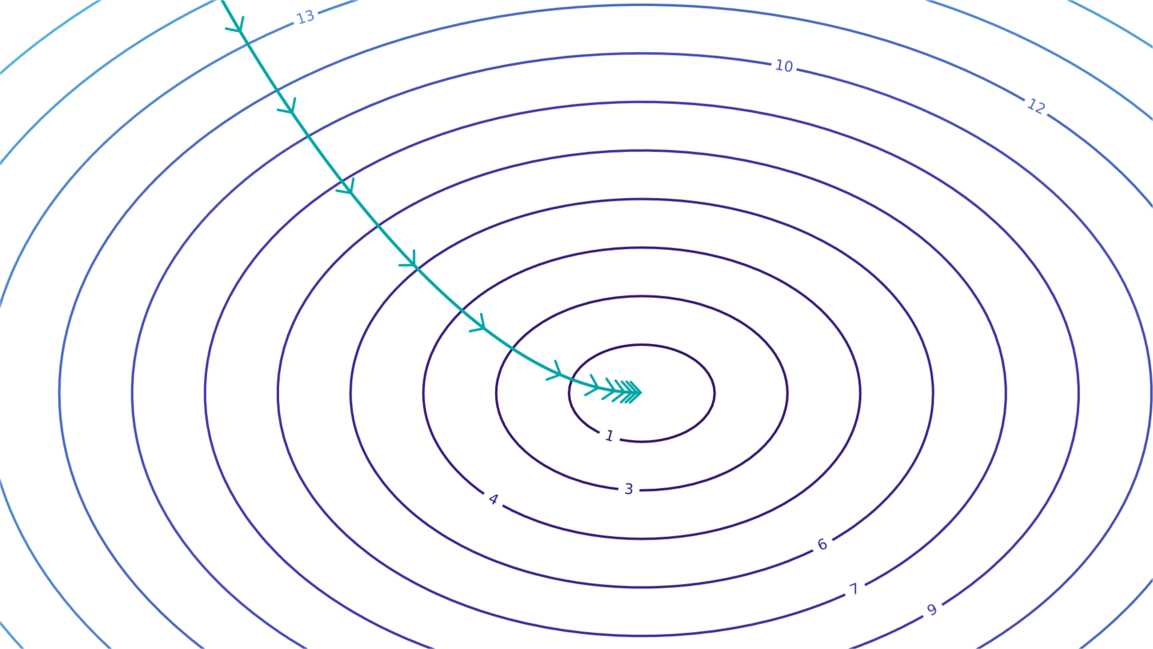
Global Tech Talent Map: Hot Tech & Job Locations
HNHIRING's latest job trends report paints a picture of the global tech talent landscape. It lists the hottest programming languages, tech stacks, and job locations. The report reveals high demand for talent in cloud computing, AI, and big data, with North America, Europe, and parts of Asia emerging as tech talent hubs. This report is a valuable resource for job seekers and companies alike, offering insights into market demand and talent distribution.
Read more