Simulating the Hand-Drawn 'Boiling' Effect with SVG Filters
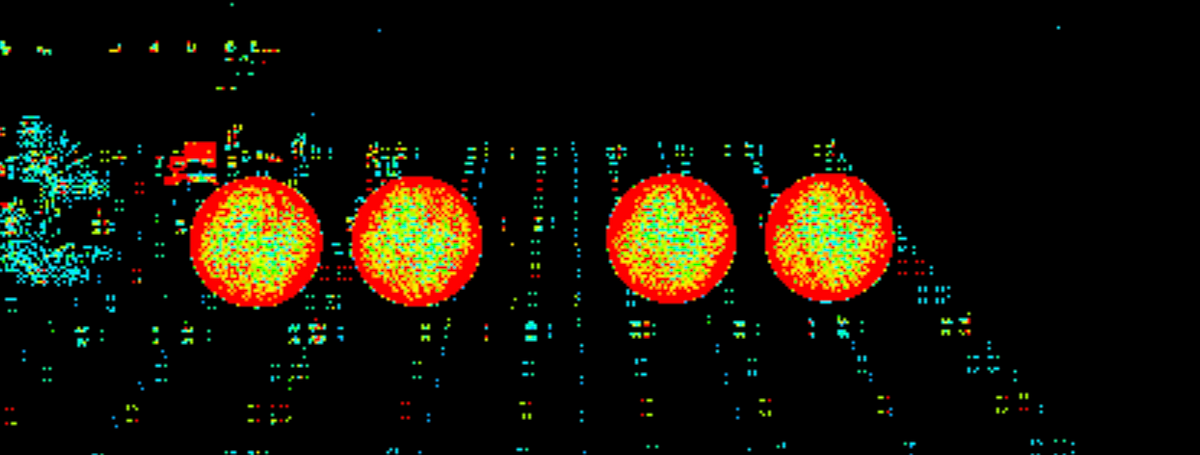
This article details a method for simulating the 'boiling' effect, a common visual style in hand-drawn animation, using SVG filters. This effect creates the illusion of subtle movement by applying slight distortions to image edges. The author explains how to use the feTurbulence and feDisplacementMap filters to generate a noise texture and apply it to an image, and how to animate filter parameters with JavaScript to achieve the boiling effect. Interactive demos allow users to adjust parameters and observe the effect's changes. The author successfully uses simple SVG filters and JavaScript to simulate a realistic hand-drawn animation effect on the web.