Screwball Scramble: Viral Hit, Copyright Takedown, and a 50-Year Legacy
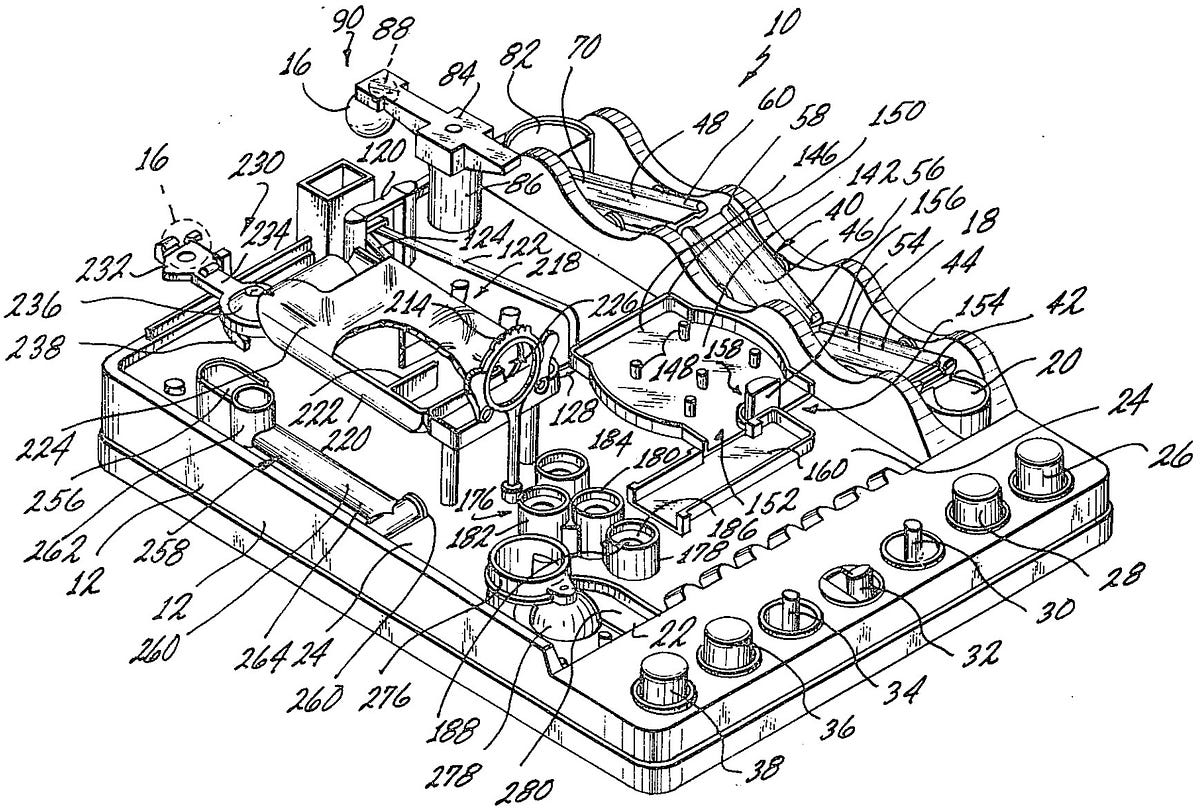
The classic toy Screwball Scramble is experiencing a viral resurgence. A humorous TikTok review by Drinks On Me garnered over 15,000 views, while a Reddit user, captainepeper, created a web-based version before being forced to take it down by TOMY due to copyright infringement. Despite this, the toy's ingenious design and challenging gameplay continue to captivate players, with Vsauce's Michael even creating a video that amassed over 12 million views. Screwball Scramble's 50-year legacy is a testament to its enduring appeal, challenging players' skill and patience, and sparking nostalgia for childhood memories and classic toys.
Read more