Capitol Riot: Parler Videos Reveal Unseen Footage
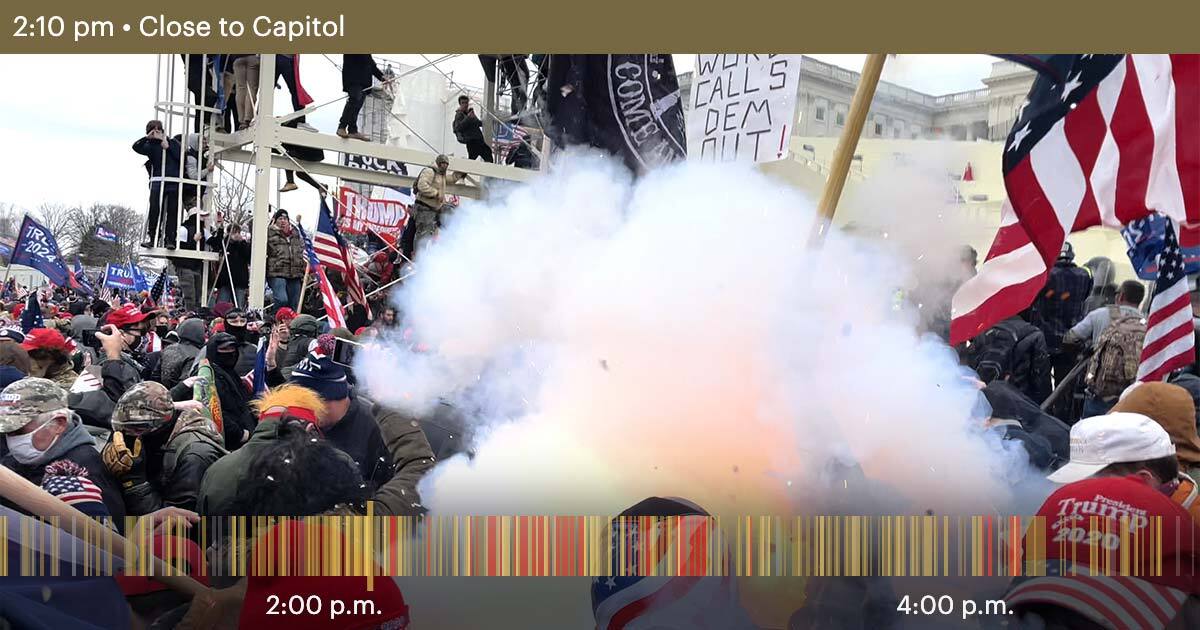
ProPublica obtained thousands of videos uploaded by Parler users during the January 6th Capitol riot. These videos, archived before Parler went offline, offer a firsthand account of the events, revealing the actions and mindset of participants. Analysis of this footage provides a more comprehensive understanding of this dark chapter in American history.
Read more











/cdn.vox-cdn.com/uploads/chorus_asset/file/25839771/1251769595.jpg)

