Hugging Face Open-Sources Two Robots: HopeJR and Reachy Mini
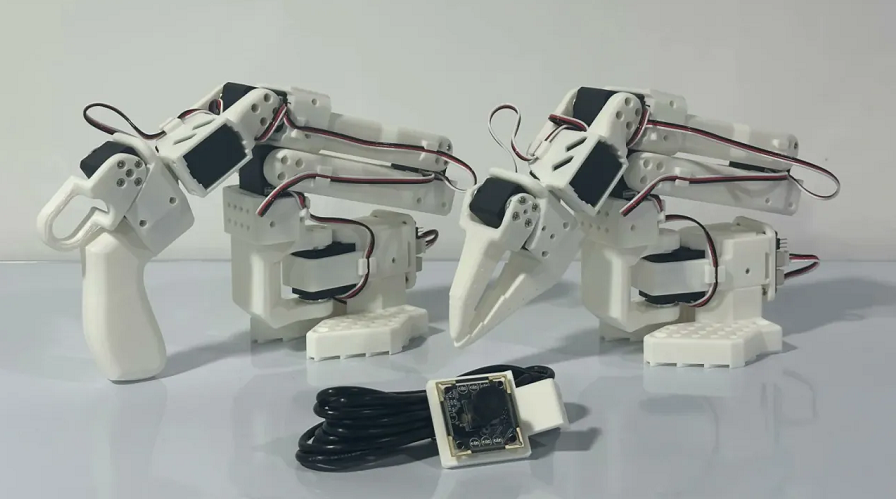
Hugging Face Inc. has open-sourced the designs of two internally developed robots, HopeJR and Reachy Mini. HopeJR is a humanoid robot capable of 66 movements, including walking, with robotic arms controlled by specialized gloves. Reachy Mini is a desk-sized, turtle-like robot with a retractable neck, ideal for testing AI applications. Blueprints for both are open-source, with pre-assembled versions selling for approximately $250 and $3,000 respectively. Shipping is expected by year's end.
Read more