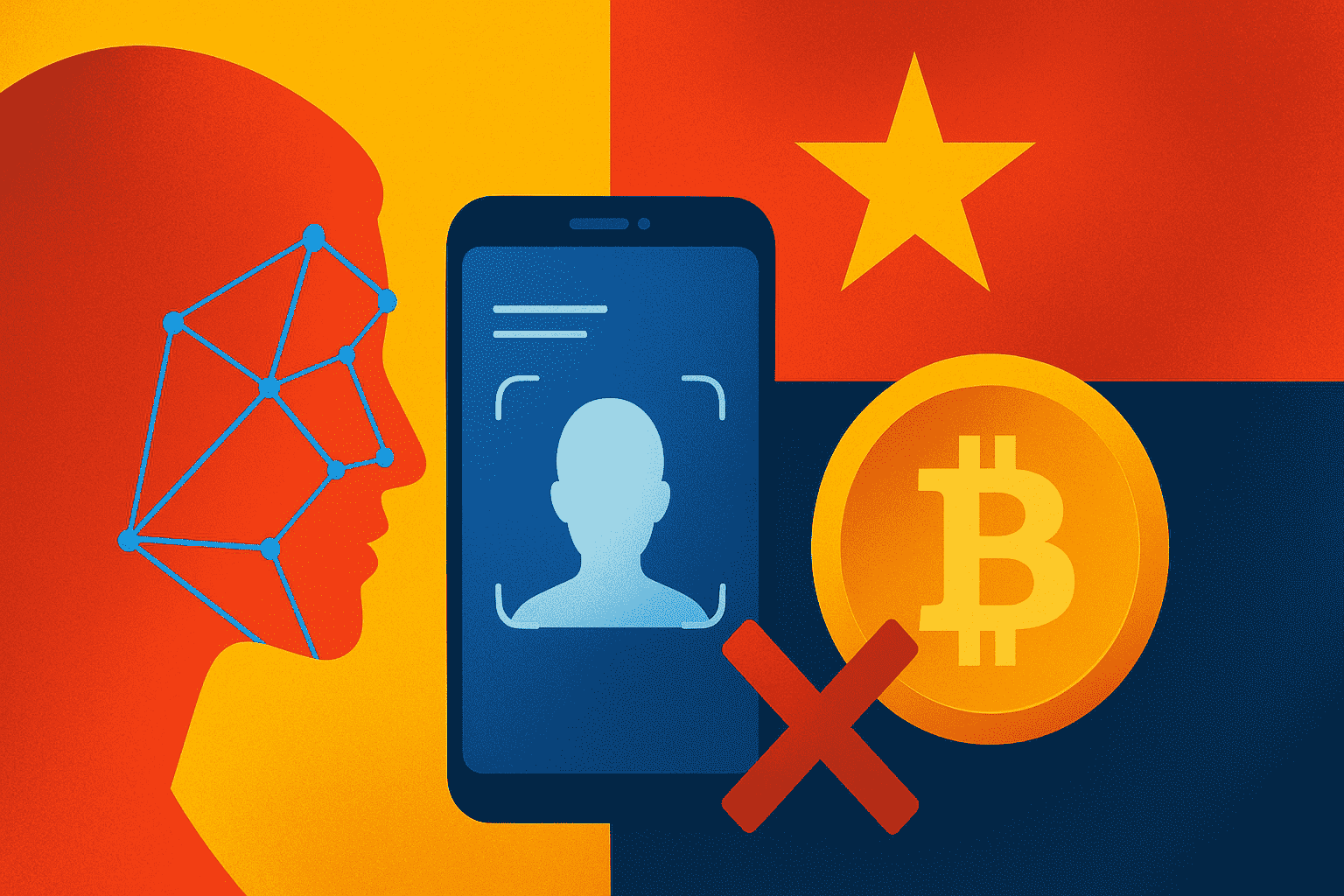
FTC Alleges Facebook Acquired Instagram to Neutralize Competition

The Federal Trade Commission (FTC) is accusing Meta (Facebook's parent company) of acquiring Instagram in 2012 to eliminate a competitive threat, not for legitimate business reasons. The FTC lawyer argued that Facebook, struggling with the shift to mobile and its own mobile photo app development, saw Instagram's rise as a major threat. A key piece of evidence is a Zuckerberg email stating the need to "neutralize a potential competitor." The FTC also points to Facebook shelving its own Facebook Camera app after the acquisition. The case hinges on whether Meta abused its market dominance, potentially leading to a breakup of Facebook.
Read more