How I Use LLMs to Supercharge My Engineering Workflow
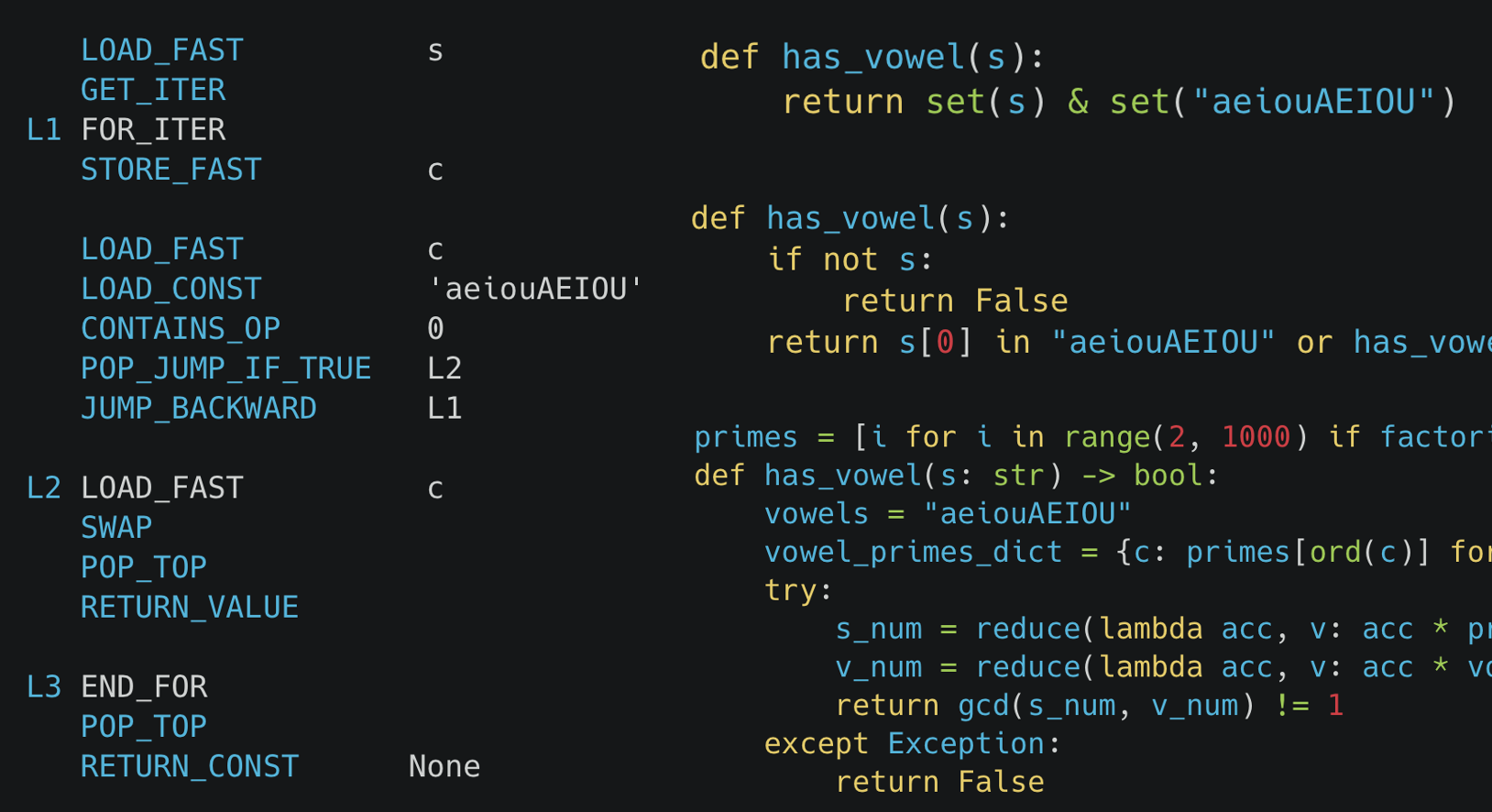
A senior software engineer shares his practical applications of large language models (LLMs) in his daily workflow. He leverages LLMs for code completion, writing throwaway code, learning new domains, last-resort debugging, and proofreading documents. He stresses LLMs are not a replacement for core logic or formal writing but a powerful aid, particularly effective for tackling unfamiliar codebases or learning new technologies. The key is using them strategically, not expecting miracles.
Read more