Deep Research: Hype Cycle or Paradigm Shift?
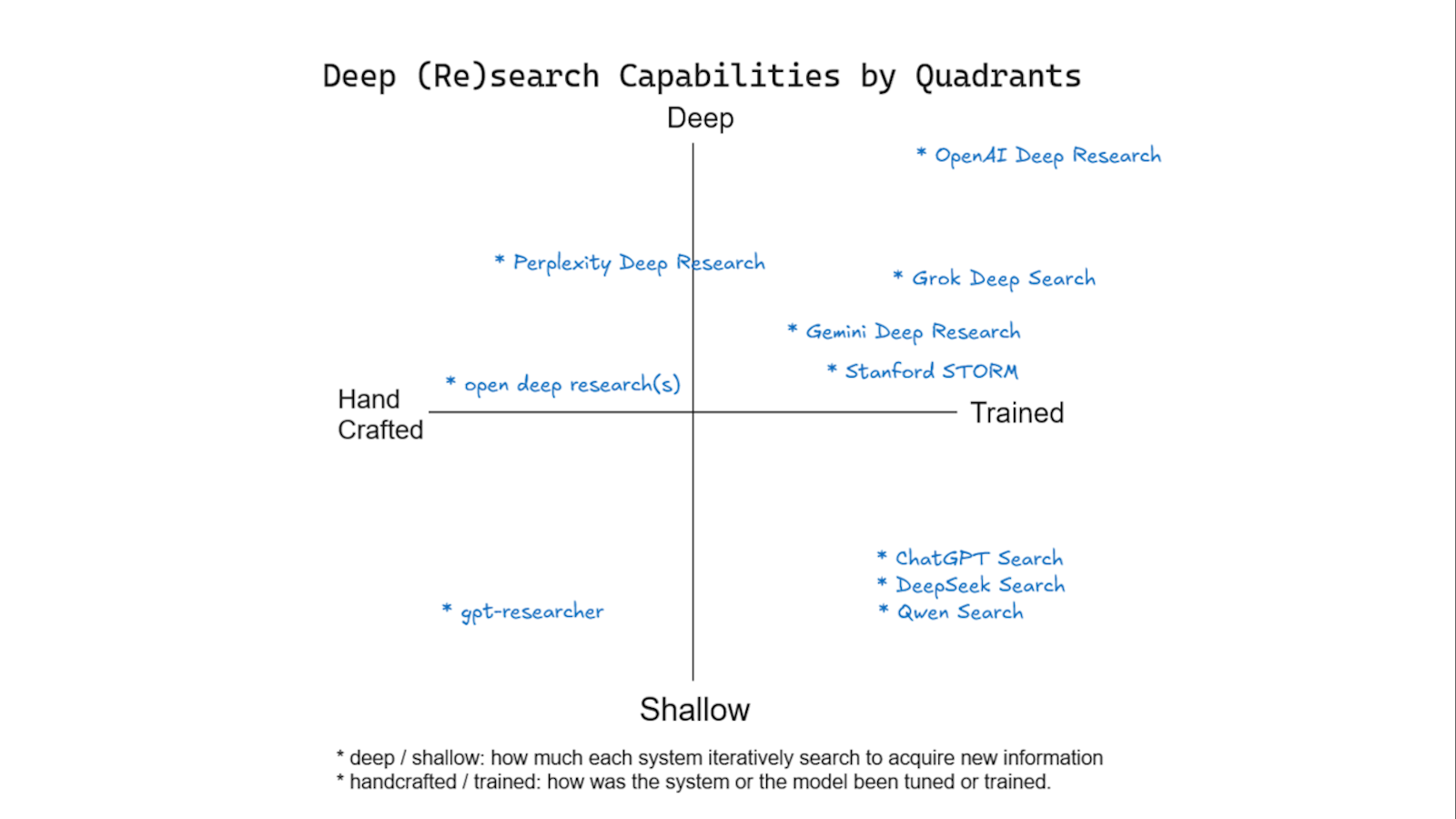
A flurry of "Deep Research" features from leading AI labs—Google, OpenAI, Perplexity, and others—has ignited a buzz. However, the term lacks a clear definition, essentially representing an evolution of Retrieval-Augmented Generation (RAG). These systems leverage LLMs as agents, iteratively searching and analyzing information to produce comprehensive reports. This article dissects the technical implementations, ranging from early composite pattern approaches with hand-tuned prompts to end-to-end optimized systems like Stanford's STORM, which utilizes reinforcement learning. While Google Gemini and Perplexity offer similar features, details remain undisclosed. The article concludes with a conceptual map comparing the iterative depth and training sophistication of various "Deep Research" offerings.
Read more