Deconstructing Zork: A Deep Dive into 15,000 Lines of 80s Game Dev
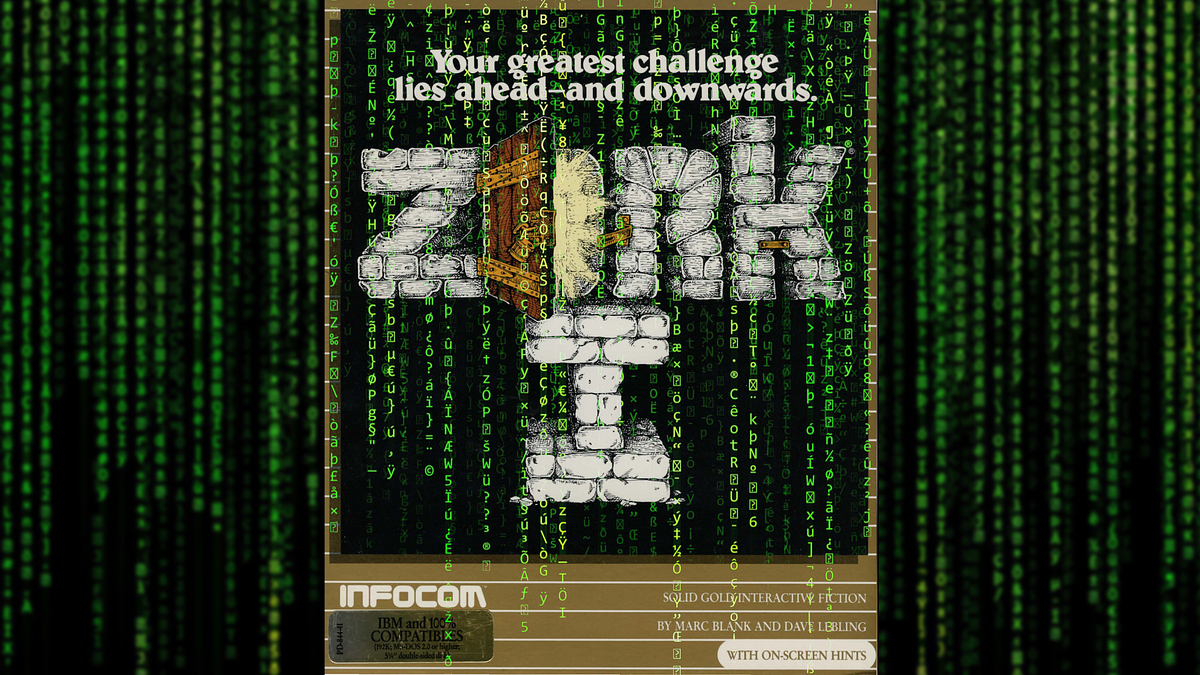
Rok Ajdnik, in a whimsical quest to test a Kubernetes cluster, embarked on a journey through the 15,000 lines of code that comprise the classic text adventure game, Zork. This article details Zork's evolution across different versions, its ZIL programming language, and its ingenious architecture, including the parser, game objects, syntax, and object tree. Hidden gems are unearthed, such as easter eggs (XYZZY), questionable commands (RAPE), and intentionally trollish mechanics. The author also shares progress on porting Zork to Go.
Read more
/https%3A%2F%2Ftf-cmsv2-smithsonianmag-media.s3.amazonaws.com%2Ffiler_public%2F1d%2Fbb%2F1dbb3045-1808-4d8f-ade1-31fb3998799b%2Fpluto_and_charon.jpg)