The Weekly Loop: A Simple Fix for Chatbot Stalls
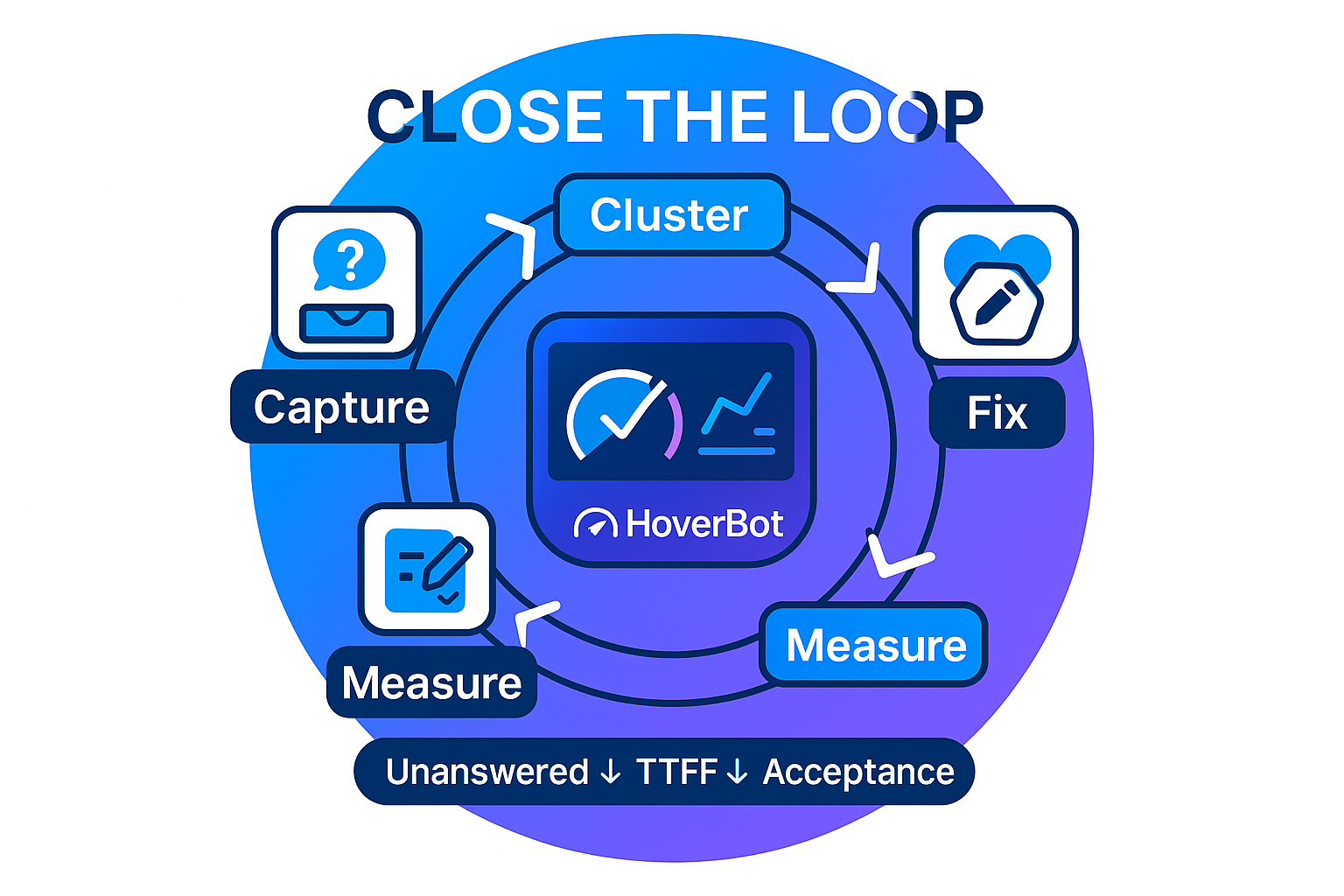
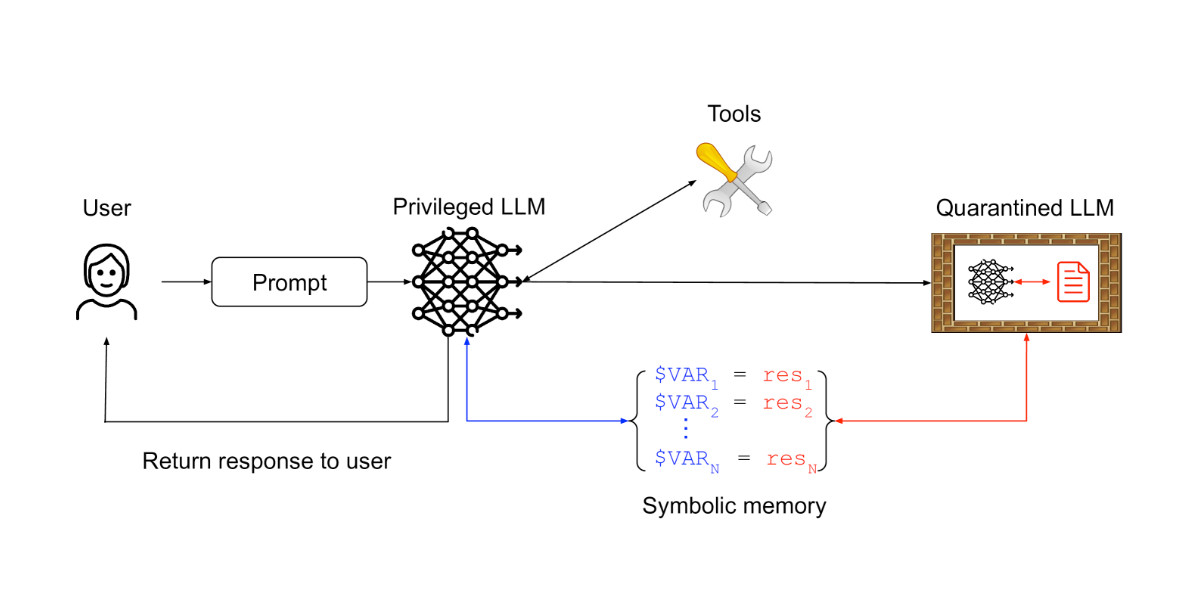
This article presents a continuous improvement methodology for chatbots, focusing on treating every miss as a signal for iterative refinement. The core concept involves a weekly loop: implement lean instrumentation to track user queries, assistant decisions, sources, answers, and fallbacks; define clear rules for unanswered questions, separating noise from genuine gaps; review the unanswered queue weekly, grouping similar issues and applying remedies (strengthening guardrails or updating the knowledge base); and finally, establish clear ownership and measure key metrics (unanswered rate, time-to-first-fix, acceptance rate). Consistent iteration leads to significant performance improvements without requiring larger models.
Read more