China's Ambitious Space Program Challenges NASA's Dominance
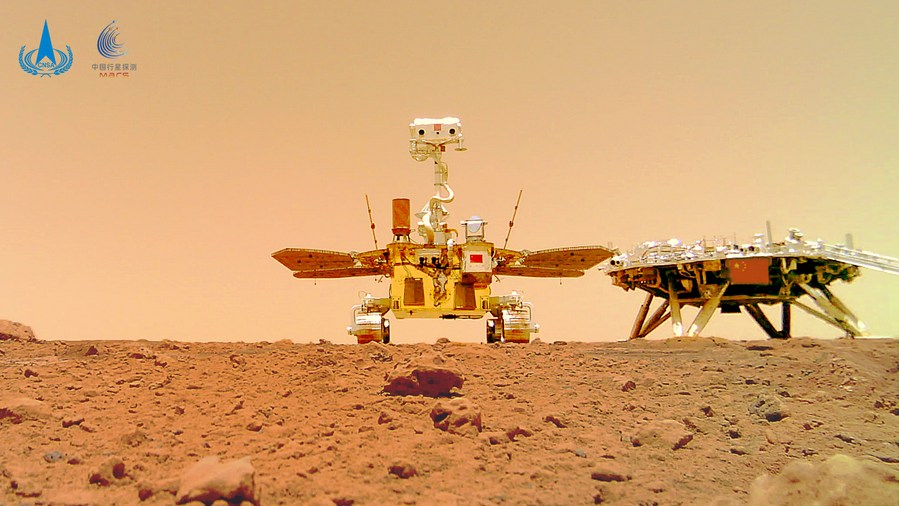
Amidst potential budget cuts at NASA, China's ambitious space program presents a compelling challenge to US leadership in space exploration. While China has achieved significant successes, its ambitious objectives are technically demanding and may face setbacks. Simultaneously funding both crewed lunar missions and robotic exploration requires substantial resources. Success, however, would greatly enhance China's international standing. NASA isn't without options; Congress may block drastic budget cuts, and cheaper satellite launch technologies could enable more deep-space exploration with less funding. The ultimate victor remains uncertain, but for the first time since the 1960s, NASA has a credible competitor.
Read more