Revolutionizing Fine-Grained Authorization: Feldera's Incremental Compute Engine
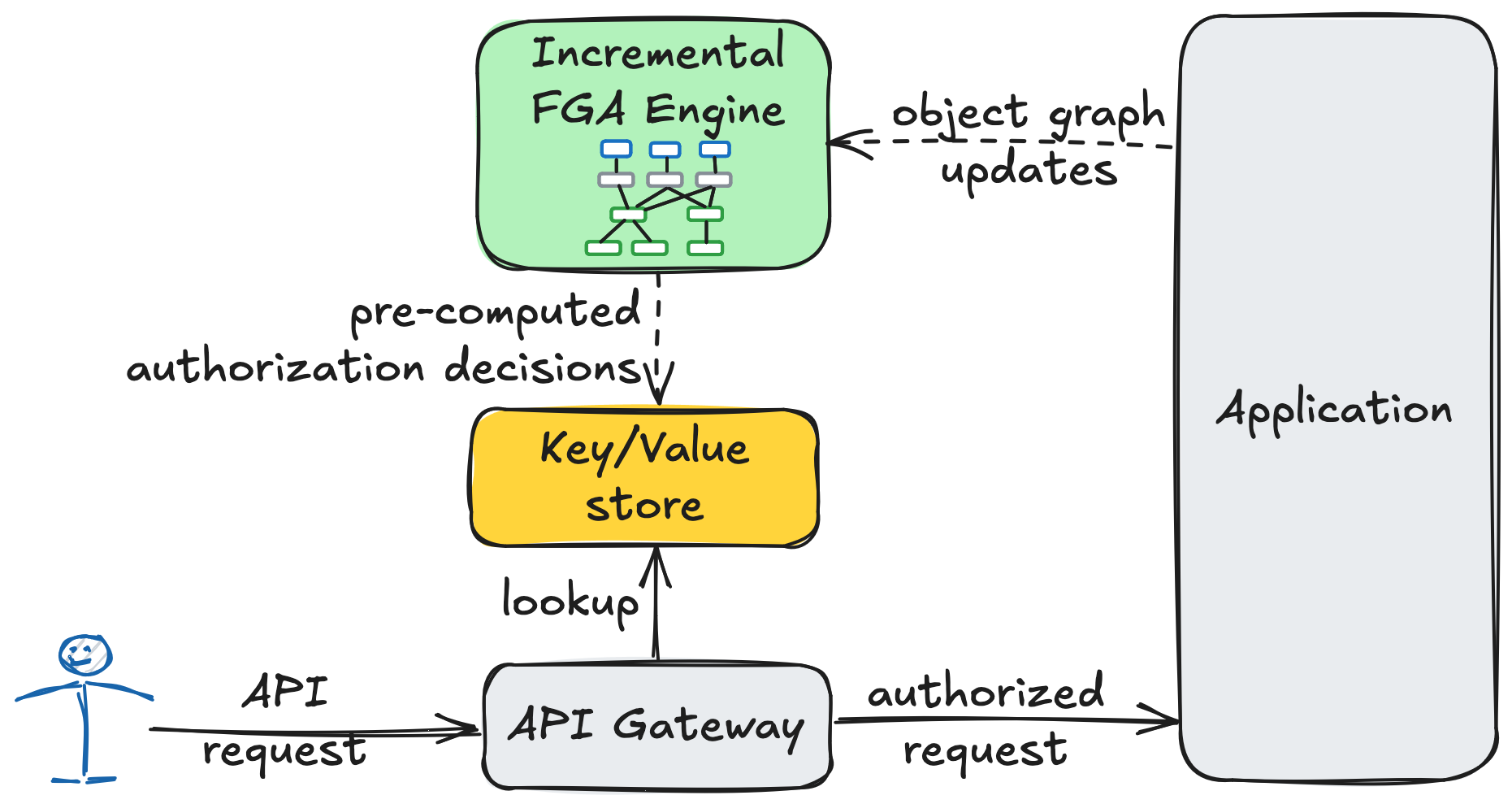
Feldera introduces a revolutionary approach to Fine-Grained Authorization (FGA). Traditional FGA systems evaluate authorization requests in real-time, leading to inefficiency. Feldera precomputes all authorization decisions and uses its incremental compute engine (based on SQL) to update results, turning authorization requests into simple key-value lookups. Even with large object graphs, Feldera processes changes in milliseconds, dramatically improving performance. The article details FGA principles and demonstrates building a high-performance FGA engine using SQL, showcasing its superiority in handling large datasets.
Read more