How Interruptions Impact Software Engineers: A Research Deep Dive

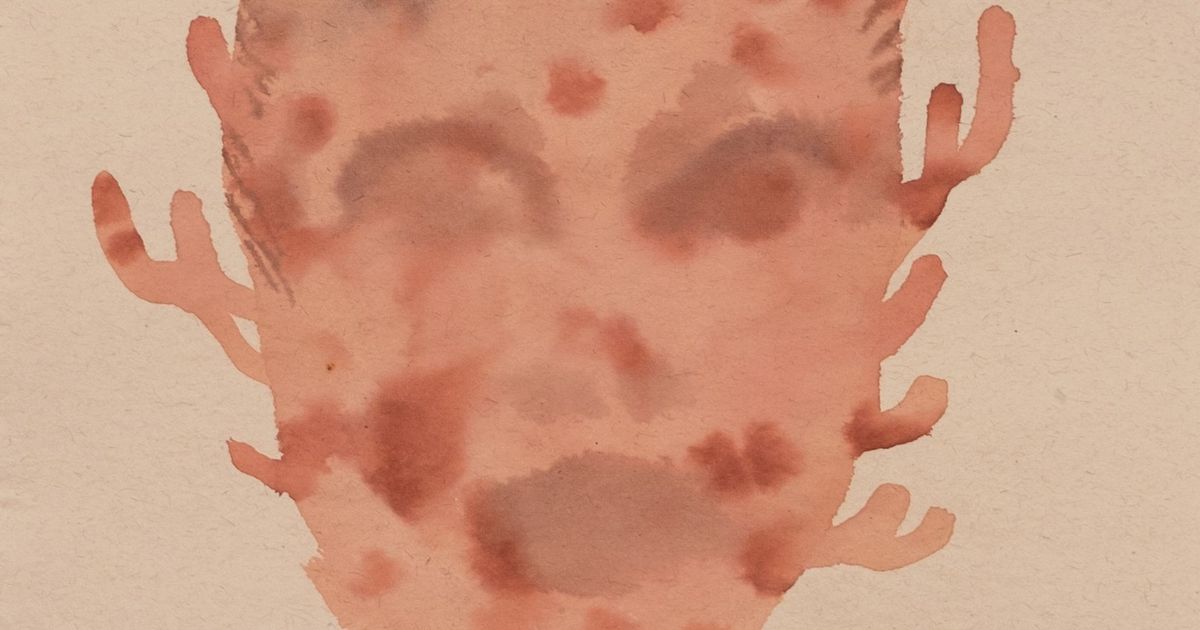
New research explores how interruptions affect software engineers' productivity and stress. The study found that different types of interruptions (e.g., in-person vs. on-screen notifications) impact coding, code comprehension, and code review differently, with complex tasks being less affected. Interestingly, physiological data (heart rate variability) showed less stress with in-person interruptions, but engineers perceived them as more stressful. Managers should prioritize engineers' perceived stress, minimizing high-priority interruptions and providing focused time for tasks like coding to boost team efficiency.
Read more