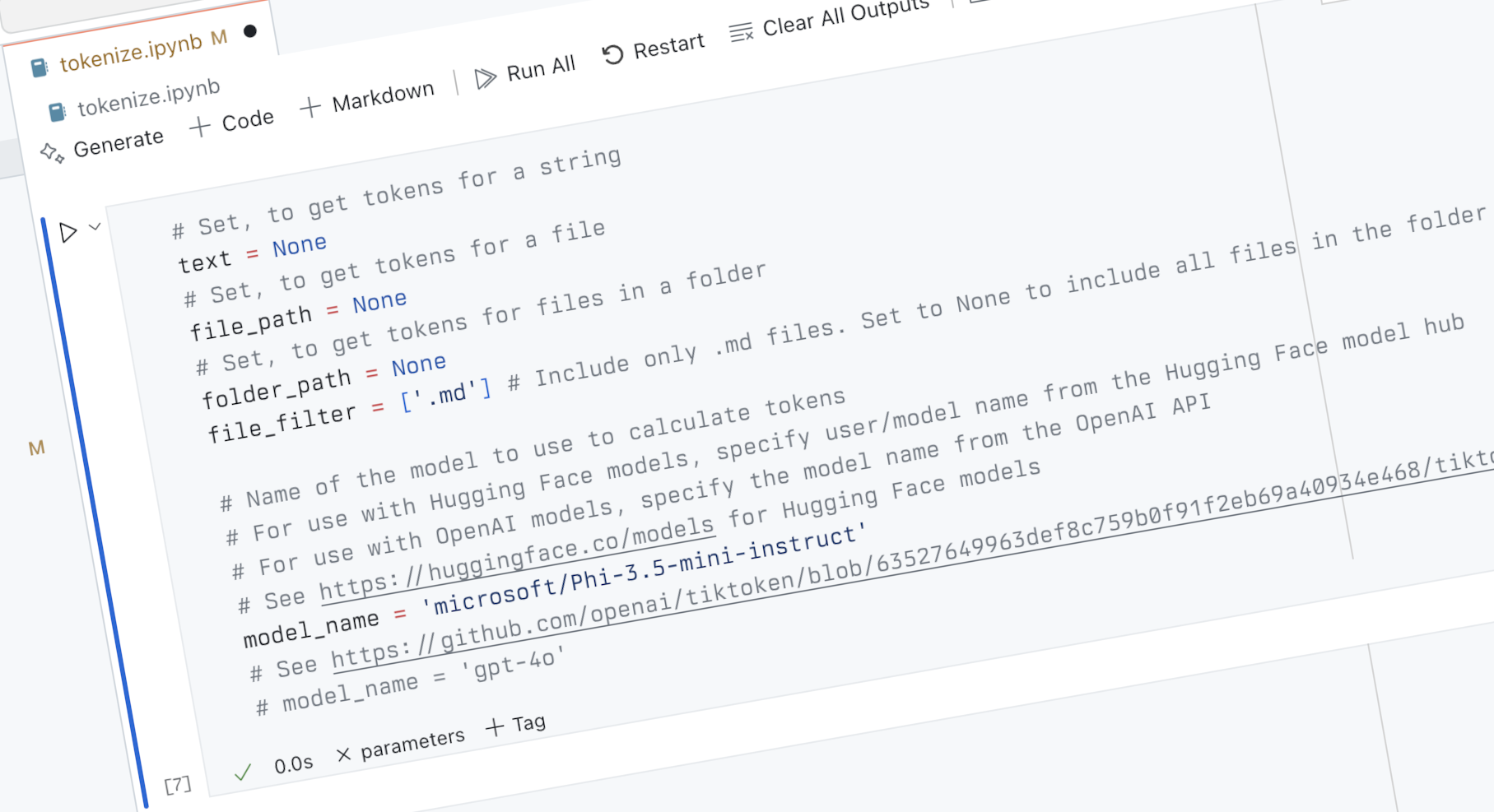
Okta Security Incident: Exploiting Bcrypt's Length Limitation

The Okta security incident stemmed from how its Bcrypt implementation handled input length. Bcrypt's 72-character limit caused truncation, allowing authentication with only partial usernames and cached keys. The article analyzes Bcrypt libraries in Go, Java, JavaScript, Python, and Rust, revealing many lack input length validation, creating security risks. The author advocates for improved API design, explicitly rejecting invalid input to prevent such vulnerabilities.
Read more