AMD's Versal RF Series: Revolutionizing RF Signal Processing with Integrated Direct RF-Sampling
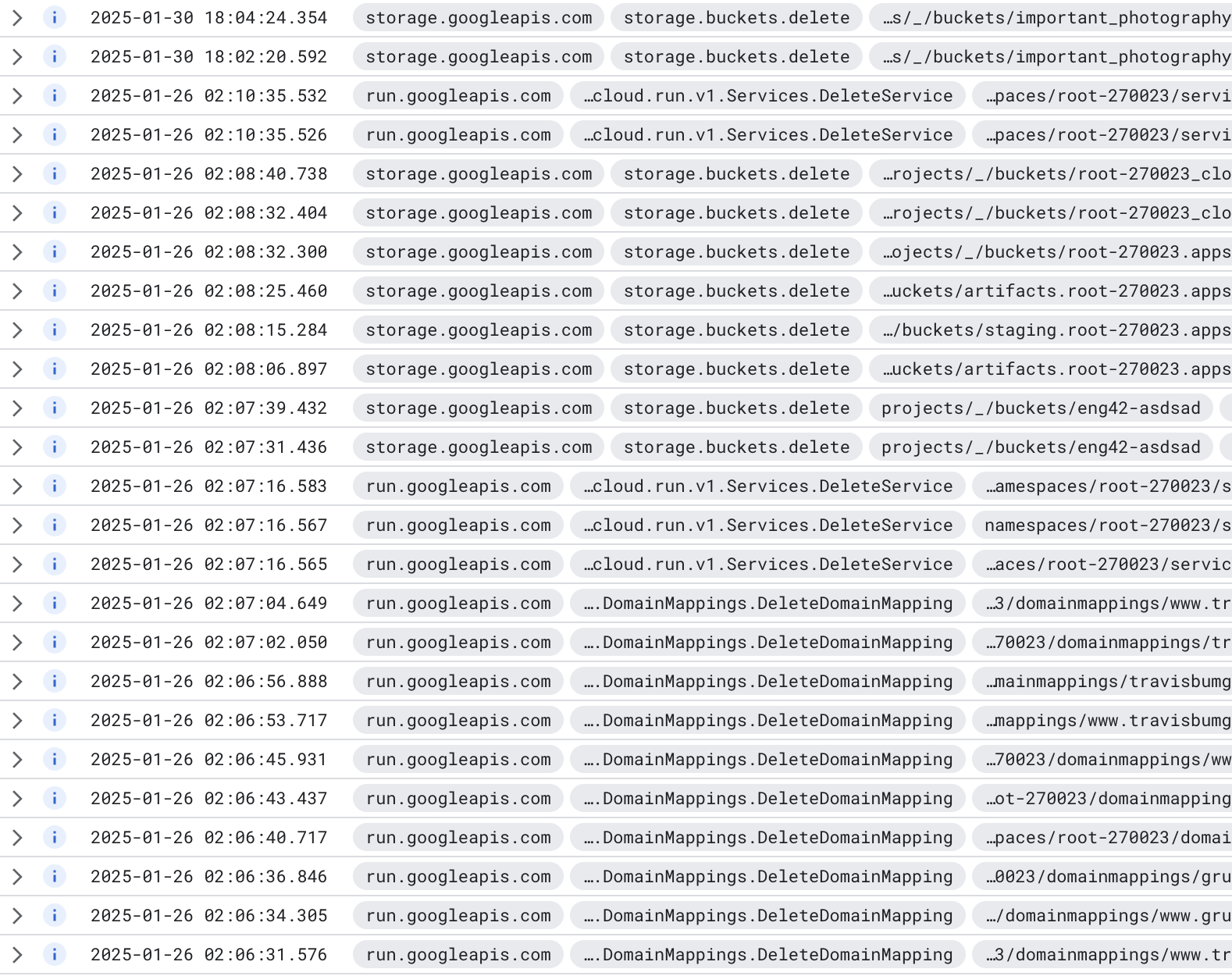
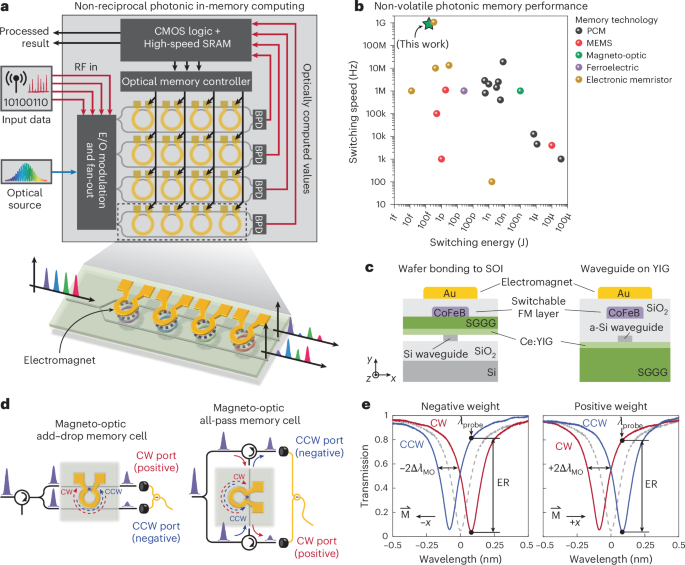
AMD is revolutionizing RF signal processing with its new Versal RF Series adaptive SoCs. These chips integrate high-resolution RF data converters, hard IP DSP compute blocks, and AI engines onto a single die, delivering up to 80 TOPS of DSP performance and 32 GSPS sample rates. Targeting aerospace & defense and test & measurement markets, the Versal RF Series boasts 19x more DSP compute and 80% lower power consumption compared to its predecessor. Its high-resolution, wideband spectrum observability and low-latency processing make it ideal for applications like phased array radar, electromagnetic spectrum operations, and military satellite communication terminals.
Read more