Mozilla's Free AI Text Detector: Fakespot Deepfake Detector
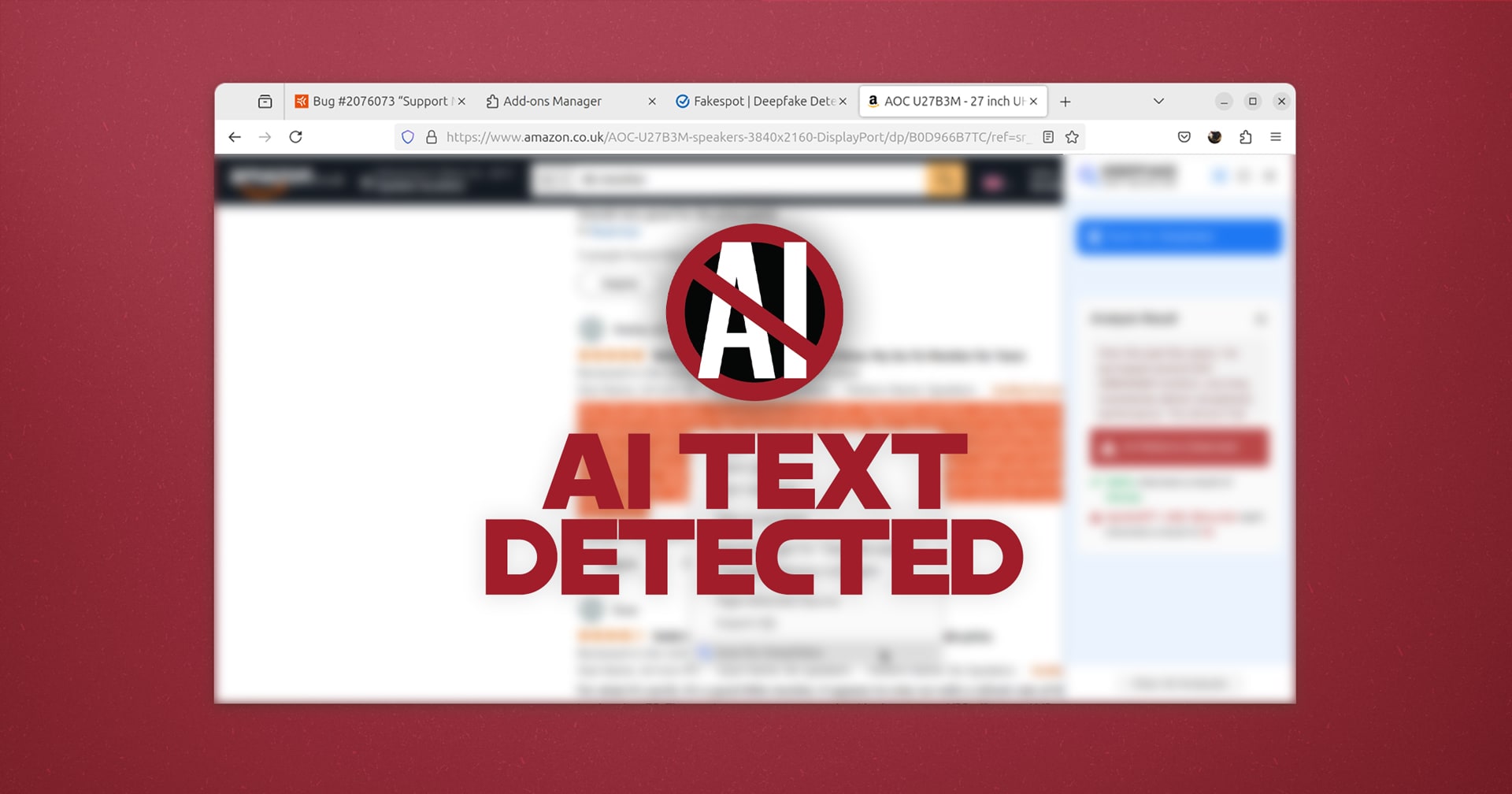
Mozilla's Fakespot has released a free Firefox add-on, Deepfake Detector, designed to identify AI-generated text online. This tool analyzes text snippets (32 words or more) for patterns indicative of AI authorship. Unlike many AI detectors, it requires no signup or app download; simply highlight text for instant analysis. While not foolproof, it offers a useful way to distinguish between human-written and AI-generated content, particularly for those seeking authentic human perspectives.
Read more