Positron: The Next-Gen Open Source IDE for Data Science

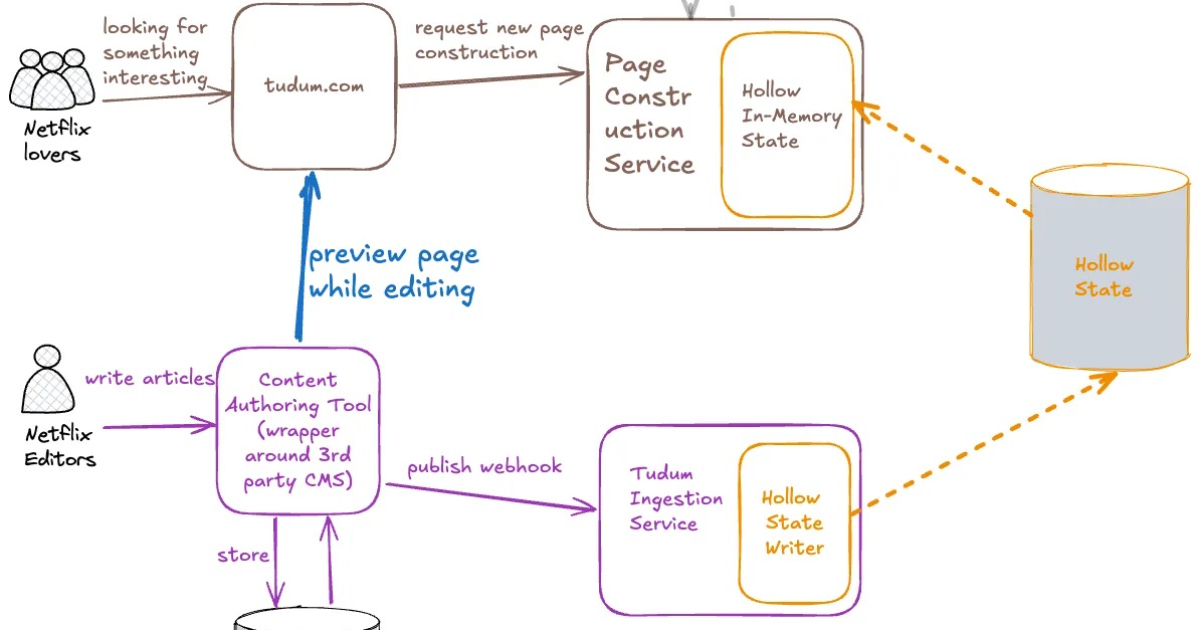
Posit PBC has launched Positron, a free, next-generation Integrated Development Environment (IDE) for data science. It seamlessly integrates data exploration and production workflows, supporting both Python and R equally. Key features include interactive notebooks, plotting tools, integrated data app workflows, and a built-in AI assistant. Built on Code OSS, Positron supports VSIX extensions for enhanced customization.
Read more