Rope: From Mocha Dick to Industrial Production
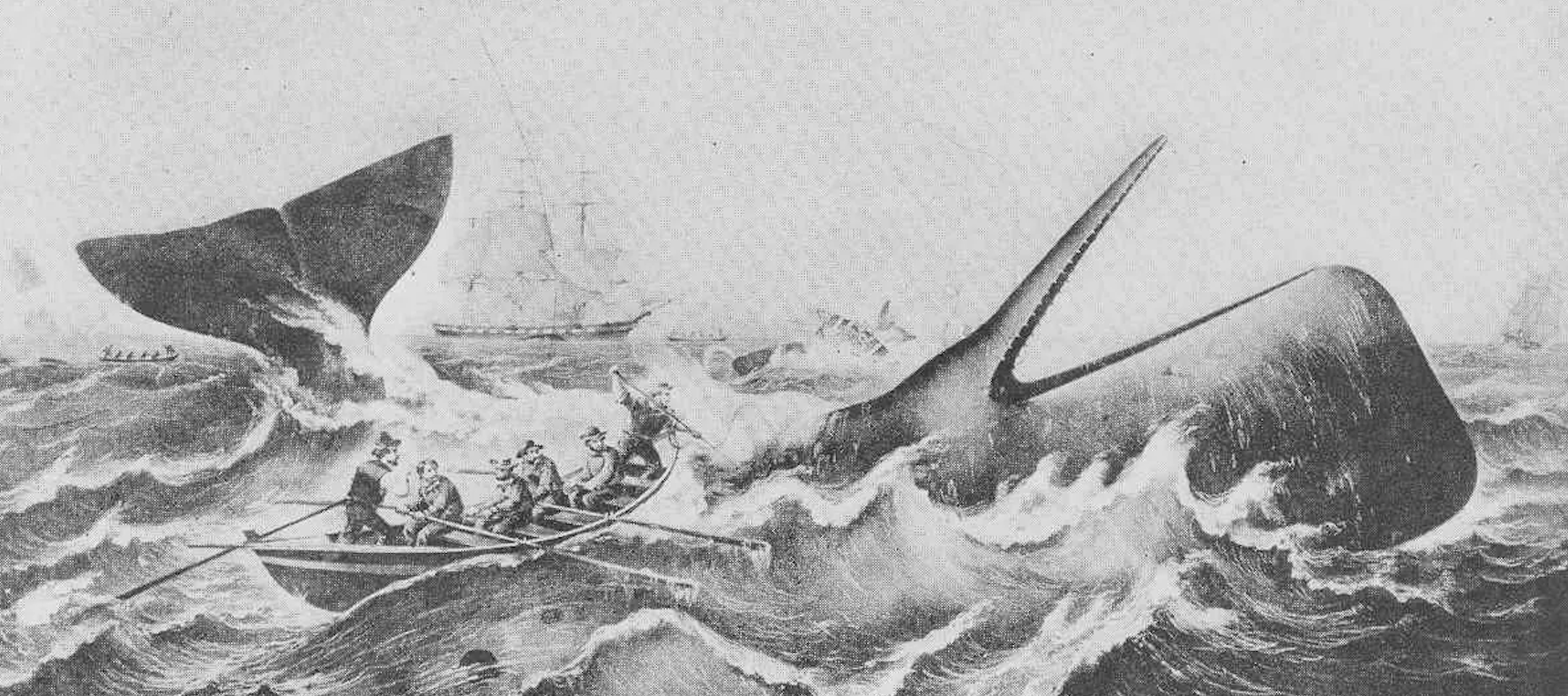
This article explores the crucial role of rope in maritime history, particularly in whaling, and its evolution towards industrial production. Starting with Jeremiah Reynolds' 1839 account of the legendary white whale "Mocha Dick", it highlights the immense demand for rope in the whaling industry. The article details the 18th-century revolution in rope-making technology, including the invention of the register plate and forming tube, the rise and development of ropewalks, and concludes by emphasizing rope's importance as "naval stores" and its indispensable role in seafaring and shipbuilding.
Read more