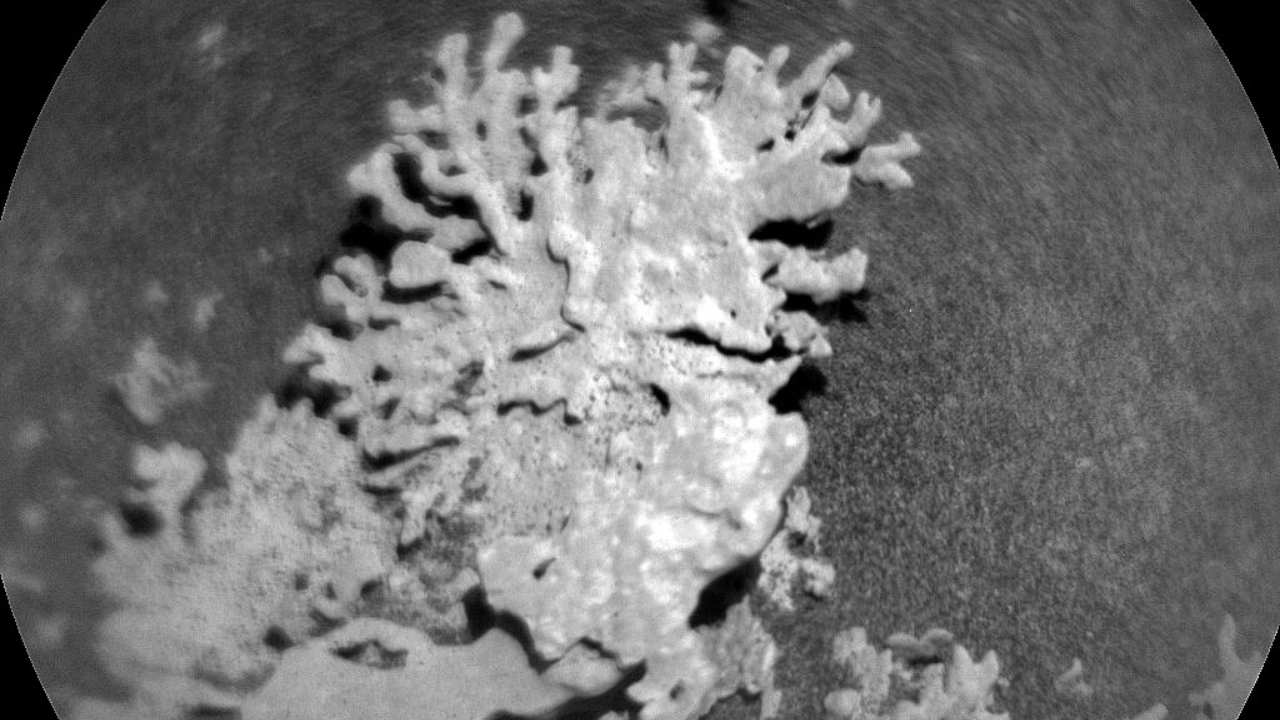
AI Copyright Wars: A Nightmare for News Orgs?

The copyright lawsuits between Getty Images and Stability AI have sparked concerns within the news industry. The author discovered their colleague's photos were used without permission to train an AI model, highlighting the potential exploitation of news organizations' content by AI companies. While some news outlets have licensing deals with AI firms, these deals may undervalue the content, leaving news organizations vulnerable to being 'drained' by AI companies. The author calls for fair compensation for news organizations and copyright holders and urges AI companies to respect intellectual property.
Read more