Tracing Myanmar's Military Command Chains: A Data-Driven Case Study
DOT • STUDIO partnered with the Security Force Monitor (SFM) to build "Under Whose Command," a platform leveraging cutting-edge technology to precisely trace Myanmar's complex military command chains. Employing sophisticated data modeling (EAV and Datalog databases) and precise handling of time and location, the platform overcomes the challenges of dynamic and overlapping command structures, providing journalists, courts, and researchers with a powerful tool for accountability. The project successfully integrated existing research workflows with new technologies, resulting in a user-friendly and sustainably maintained public platform.
Read more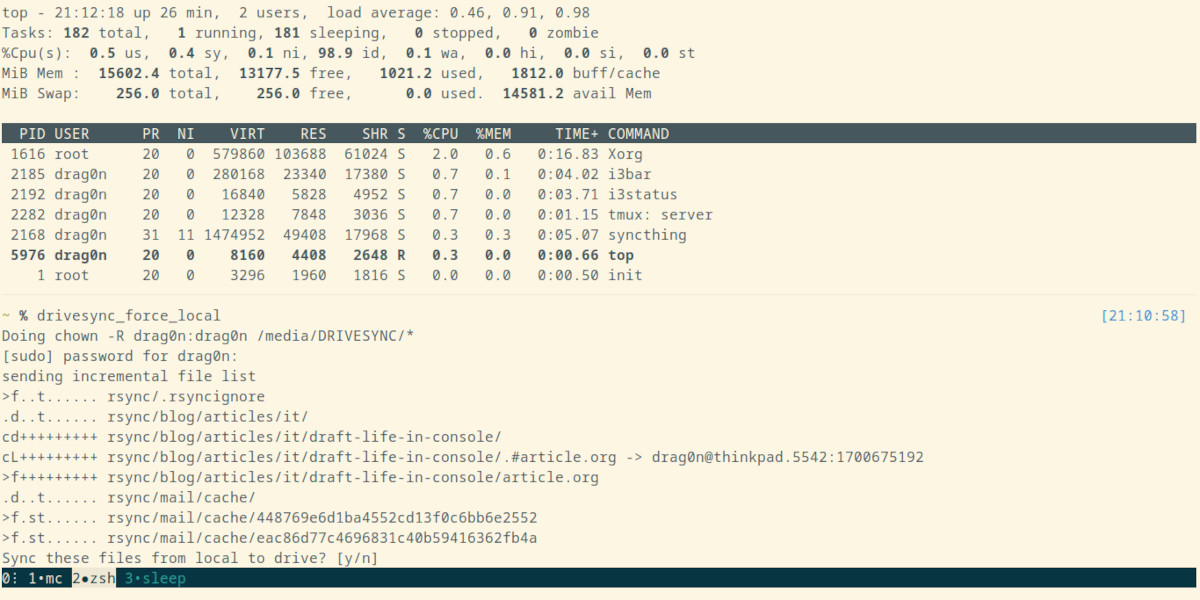






/cdn.vox-cdn.com/uploads/chorus_asset/file/25839771/1251769595.jpg)






