libobscura: Tackling the Challenges of Camera Programming on Linux
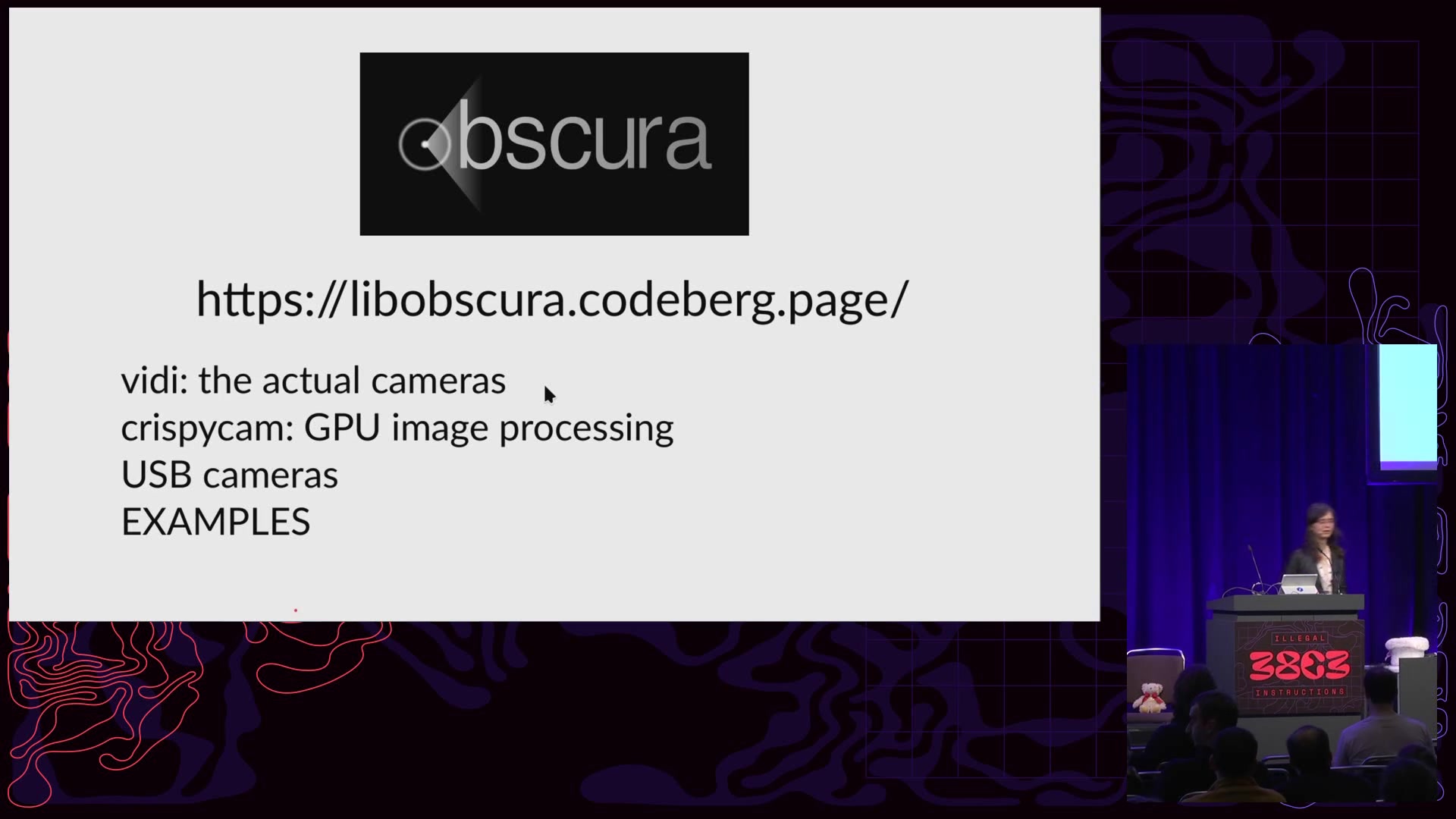
Using cameras on Linux isn't easy, leading to the creation of libobscura. This project aims to simplify the Video4Linux interface, providing a user-friendly point-and-shoot API. Born from experience developing the camera stack for the Librem 5 and addressing the complexities of libcamera, the talk dives into the intricate details of modern camera control. From pixel formats and depths to media entities, sensitivity, denoising, and more, the challenges are numerous. Funded by the Prototype Fund, libobscura seeks to navigate these complexities, ultimately creating a more accessible camera API for Linux users.
Read more