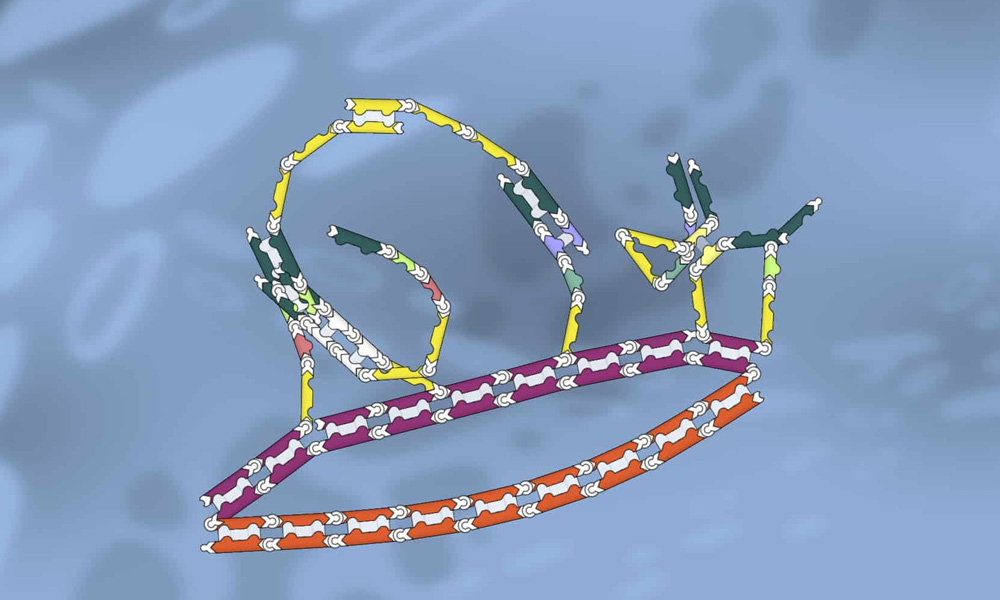
Bambu Lab, a 3D printer manufacturer, has launched CyberBrick, a new toy system under its MakerWorld brand. CyberBrick combines reusable, programmable electronics with 3D-printable models, enabling a wide range of toys based on official and community designs. Initially a Kickstarter exclusive, it's already exceeded its funding goal, with kits shipping in May 2025. The system launches with three official toys (forklift, truck, soccer bot) and a wireless controller. Kits, starting at $29.99, include solderless electronics and instructions for 3D printing. Pre-printed parts are available on Kickstarter but won't be offered through Bambu's Maker's Supply store. Beyond the official toys, CyberBrick boasts community designs like a lunar rover and a Tesla Cybertruck replica, showcasing its expandable nature. The system even extends beyond toys, with components for timelapse 3D printing. Crucially, everything is programmable, opening up endless possibilities for creative construction and coding.
Read more