Cells Remember Too: Challenging the Definition of Memory
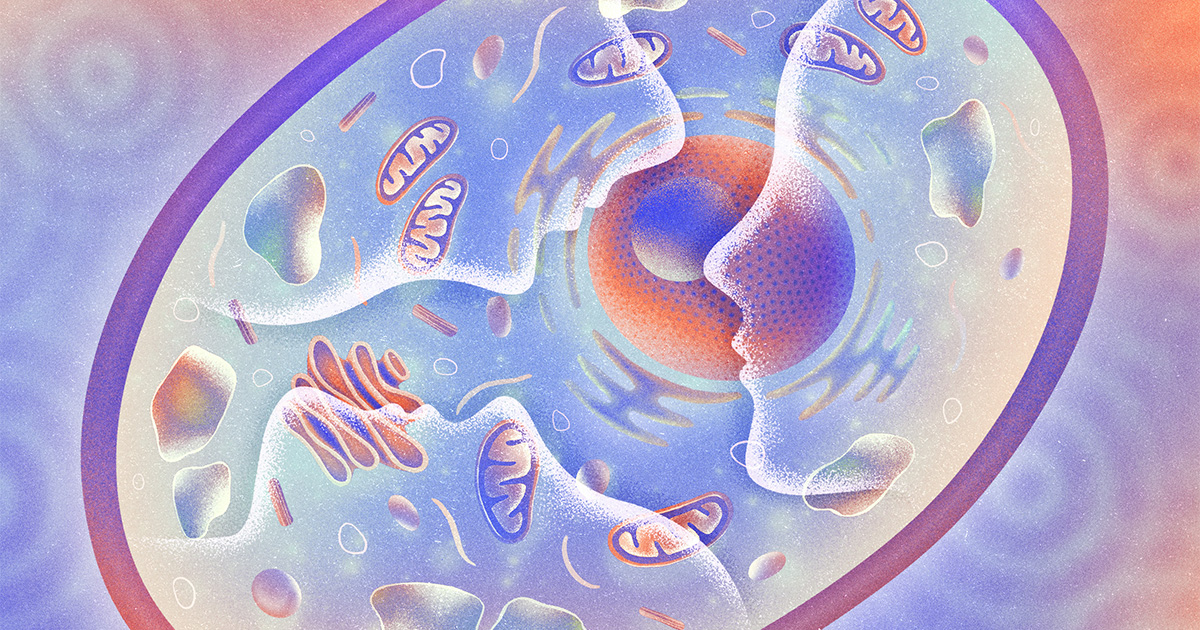
Neuroscientist Nikolay Kukushkin at NYU has found that both nerve and kidney cells can differentiate patterns of neurotransmitter bursts and form memories lasting up to a day. This suggests that even non-neural cells can perform pattern recognition and memory, challenging the traditional neuroscientific definition of memory. The research indicates that the formation of cellular memory is related to the spacing of stimuli; spaced stimuli more easily form lasting memories, similar to the mechanisms of memory formation in animals. The study also reveals long-standing biases in the scientific community, limiting memory to observable behavioral changes and ignoring cellular-level memory mechanisms.
Read more