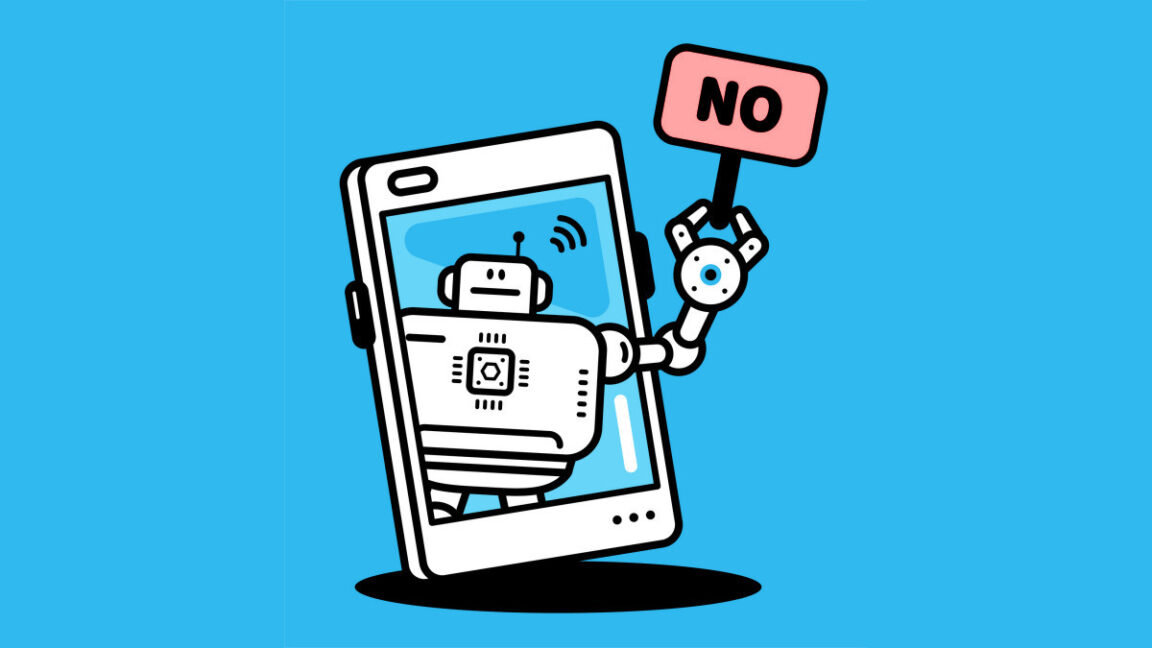
Valve Opens Team Fortress 2's Source Code to the Public

Celebrating its upcoming 20th anniversary, Valve has unexpectedly released the full client and server source code for Team Fortress 2, inviting players to modify, extend, or even rewrite the game. This move aims to empower the community and extend the life of this classic shooter. Despite recent struggles with bots, TF2 retains a dedicated player base. The open-source initiative is expected to unlock a wave of creative mods and potentially even entirely new games. However, all modifications must remain free of charge.
Read more