Spectral JPEG XL: Crushing Spectral Image File Sizes by 10-60x

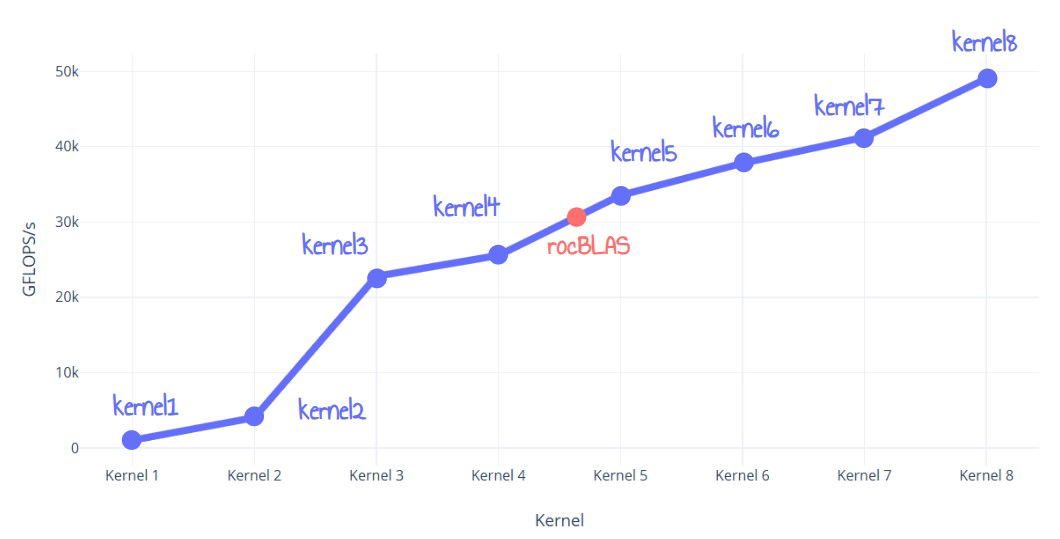
Researchers have developed a new technique leveraging JPEG XL to compress spectral images by a remarkable 10 to 60 times, shrinking them to sizes comparable to regular high-quality photos. The method prioritizes discarding less important high-frequency spectral details while preserving metadata and high dynamic range. Although lossy, this approach holds immense potential for scientific visualization and high-end rendering, addressing the storage and transfer challenges posed by massive spectral image files.
Read more