Life After the Newag DRM Disclosure: A 38C3 Report
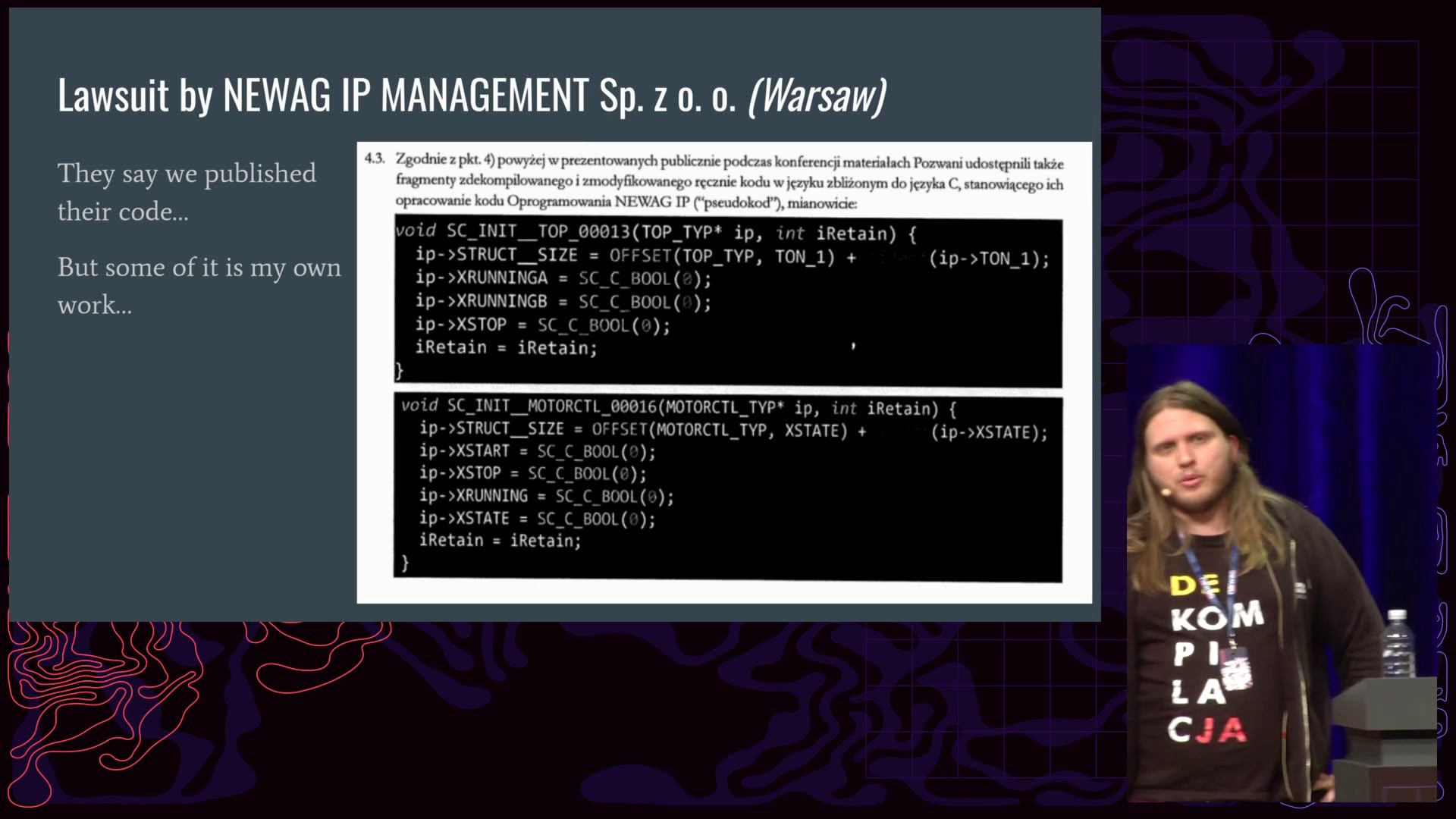
Following the disclosure at 37C3 of remote failure simulation code in Newag trains, security researchers faced a backlash. This update details the aftermath, including legal battles with Newag and train operators, media interactions, and multiple official investigations. The report also reveals new cases from different train operators, illustrating the challenges faced by security researchers when confronting powerful adversaries.
Read more