Open Source Power Plays: Rug Pulls, Forks, and the Shifting Sands of Control
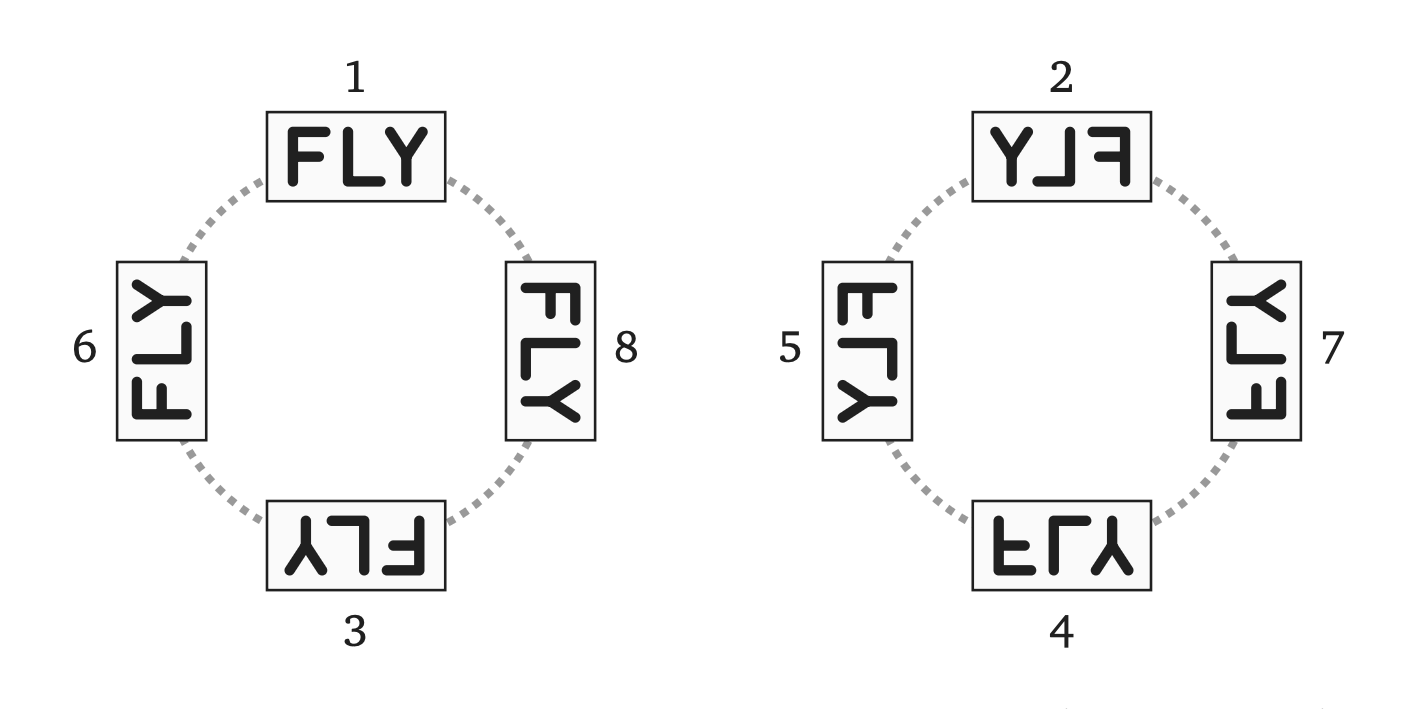
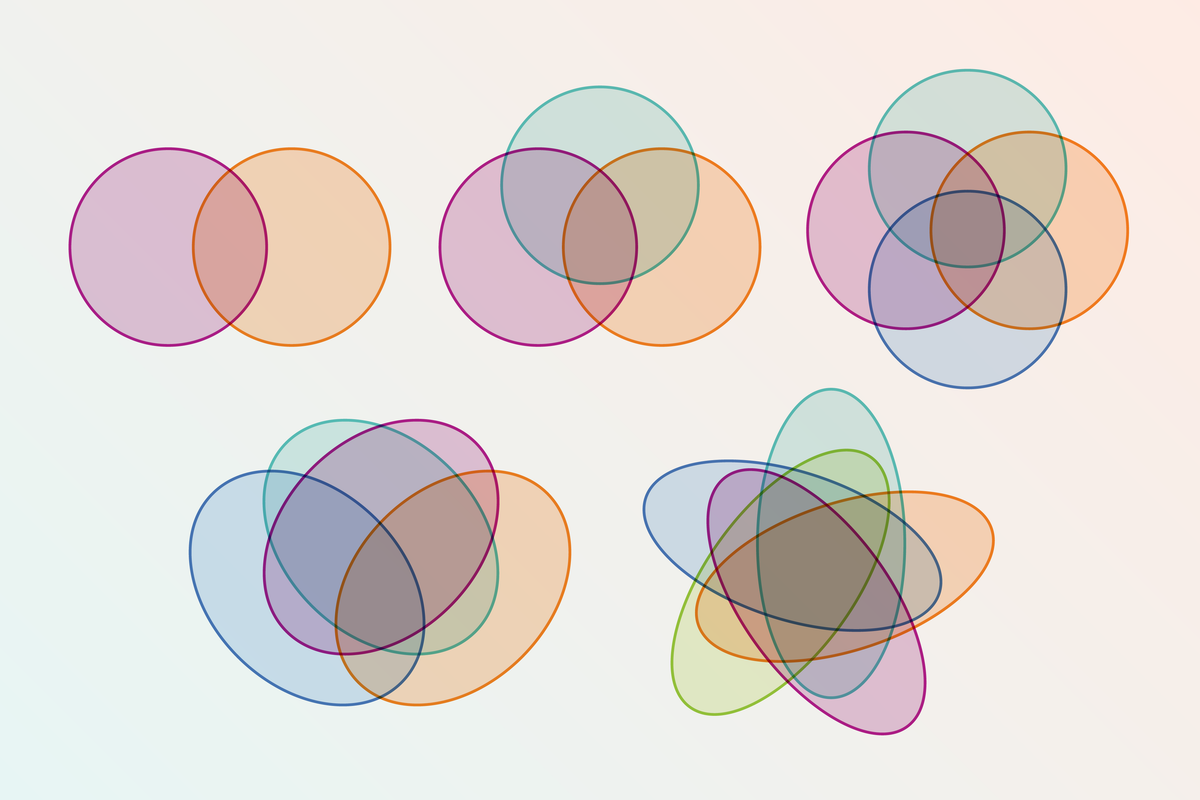
At the 2025 Open Source Summit Europe, Dawn Foster dissected the complex power dynamics in open-source software development. Large cloud providers often hold significant sway, potentially leveraging this power to the detriment of smaller companies. One tactic, 'rug pulls,' involves companies re-licensing software to restrict competitor profitability, often leading to 'forks' – community-driven project branches to regain control. The presentation analyzed case studies like Elasticsearch, Terraform, and Redis, comparing contributor composition changes before and after forks. The importance of neutral governance and a diverse contributor base emerged as key themes. Foster highlighted that while forking offers a means for maintainers and contributors to combat power imbalances, projects should prioritize neutral governance and broad contributor participation to mitigate the risk of rug pulls.
Read more